Security researchers operating honeypots are witnessing an unprecedented surge in malicious internet scanning activity, with daily log volumes reaching record-breaking levels that dwarf historical patterns.
Multiple honeypot operators report generating over 20 GB of web honeypot logs per day for extended periods, with one system capturing nearly 58 GB of activity in a single 24-hour period, obliterating the previous record of approximately 35 GB.
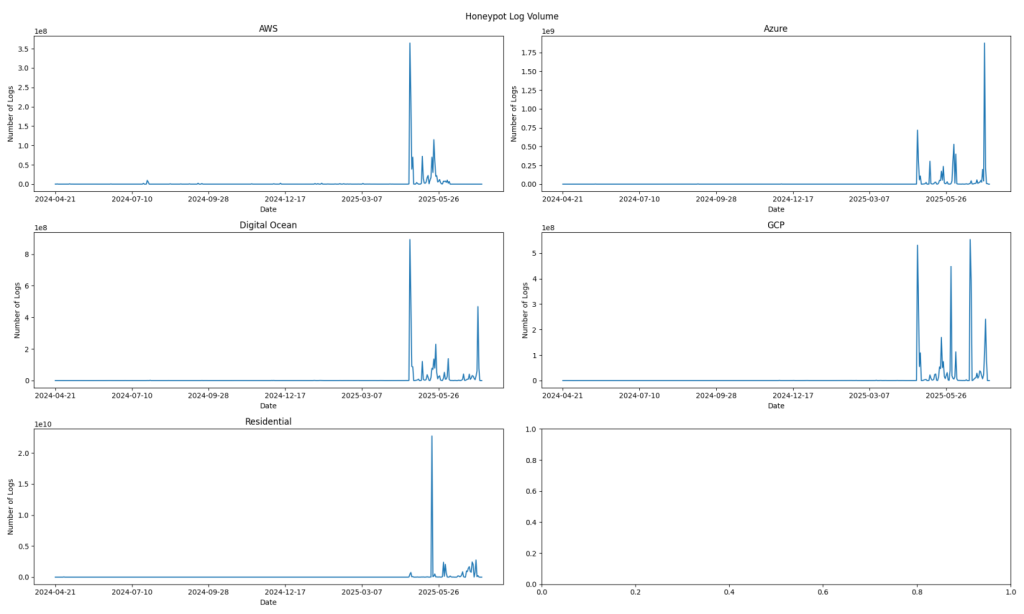
Unprecedented Volume Surge Overwhelms Historical Data
The dramatic escalation in honeypot activity has fundamentally altered the landscape of internet scanning behavior.
Recent log volumes have become so massive that they render previous high-activity periods virtually invisible on tracking charts.
To demonstrate the scale of this change, researchers found it necessary to filter out any source network contributing more than 1,000,000 logs per day just to visualize earlier traffic patterns.
The surge represents a significant departure from historical norms, where honeypots typically maintained consistent but moderate log volumes.
While occasional spikes in activity have been documented previously, the current sustained high-volume period represents an exceptional deviation from established patterns that have been intensifying in recent months.
Web Honeypots Bear the Brunt of Scanning Activity
Analysis reveals that web honeypot logs constitute the primary driver of this volume explosion.
The most targeted endpoints include the root directory (“/”) with over 38 billion hits, followed by “/api/v1/config/domains,” which generates more than 33 billion requests.
Additional high-volume targets include “/api/v1/logon”, which receives over 1.6 billion hits, as well as various API endpoints and configuration files.
Subnet-level analysis indicates coordinated scanning efforts, with specific IP ranges demonstrating focused targeting patterns.
Notable activity originates from subnets including 45.146.130.0/24, 179.60.146.0/24, and 185.93.89.0/24, each generating millions of requests while concentrating on a limited set of URL paths.
Storage Challenges Mount for Security Researchers
The sustained high-volume activity presents significant operational challenges for honeypot operators. Daily web honeypot files regularly exceed 1 GB, with multiple systems generating over 20 GB daily for consecutive days.
Researchers estimate that weekly log retention could require storing 140 GB of compressed web honeypot data between backup cycles.
To address storage constraints, honeypot operators are implementing more aggressive archival strategies, including high-compression zipping of logs potentially twice daily.
The unprecedented volume surge necessitates fundamental changes to log management practices, forcing researchers to balance comprehensive data retention with practical storage limitations while maintaining the valuable intelligence these systems provide about evolving internet threat patterns.
.jpg?w=696&resize=696,0&ssl=1)





