Cybersecurity researchers have uncovered a sophisticated banking trojan called DoubleTrouble that has rapidly evolved its attack methods, shifting from traditional phishing websites impersonating European banks to leveraging Discord channels for malware distribution.
The malware represents a significant threat to mobile banking security, employing advanced techniques to steal credentials and gain unauthorized device access.
Evolution in Distribution and Capabilities
DoubleTrouble initially spread through phishing websites targeting well-known European financial institutions, using overlay attacks to capture banking credentials and keylogging functionality.
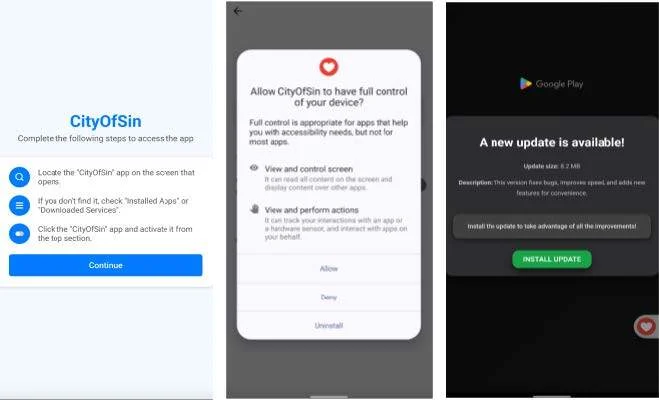
However, recent analysis by Zimperium’s zLabs team reveals the malware has undergone substantial evolution, now utilizing bogus websites that host malicious samples directly within Discord channels.
The latest iteration incorporates significantly expanded capabilities, including advanced screen capture functionality and a comprehensive suite of new commands.
Researchers have collected 25 samples from previous variants and nine samples from the current campaign, encompassing both droppers and payloads.
The malware employs sophisticated obfuscation techniques, assigning nonsensical two-word combinations to methods and class names to hinder static analysis.
Like other modern banking trojans, DoubleTrouble heavily abuses Android’s Accessibility Services to execute fraudulent activities, using a session-based installation method to bypass typical restrictions.
Advanced Attack Techniques
DoubleTrouble’s most concerning feature is its comprehensive screen recording capability, utilizing Android’s MediaProjection and VirtualDisplay APIs to create real-time mirrors of user screens.
The malware captures individual frames, converts them to JPEG format, and encodes them in base64 before transmitting to command and control servers.
This provides attackers with unobstructed views of sensitive information, including banking credentials, cryptocurrency wallets, and multi-factor authentication codes.
The malware also implements a highly sophisticated keylogger that monitors every keystroke and application change in real-time, storing captured data in files named “heart_beat.xml” within the app’s SharedPreferences.
Additionally, it can block specific applications by displaying deceptive “System Maintenance Notice” overlays, typically targeting banking or security applications as preparation for overlay attacks.
DoubleTrouble leverages open-source libraries like PatternLockView and PinLockView to create fake lock screens, stealing pattern, PIN, or password-based credentials.
The malware supports over 30 different commands from its C2 server, enabling extensive device manipulation, including notification injection, app control, and UI automation.
Detection and Protection
Zimperium’s Mobile Threat Detection and Runtime Application Protection successfully identifies both older and newer DoubleTrouble variants using on-device dynamic detection engines.
This protection remains effective even when malware uses novel distribution channels, custom obfuscation techniques, or previously unseen samples.
As threat actors continue innovating with advanced capabilities, real-time mobile threat defense becomes critical for protecting individuals and organizations from credential theft, account takeover, and financial fraud targeting mobile banking platforms.






