In June 2025, cybersecurity researchers at NSFOCUS Fuying Lab detected a powerful new botnet named hpingbot proliferating across global networks.
Distinct from legacy threats, hpingbot is coded in Go and supports a range of platforms, including Windows, Linux, and IoT devices.
Notably, it’s engineered for multiple processor architectures, ranging from AMD64 to MIPS and ARM, signaling a leap in cross-platform malicious automation.
What sets Hpingbot apart from older families like Mirai and Gafgyt isn’t just its innovation; it’s the way attackers are leveraging modern resources to lower development and operational costs.
Harnessing the text-sharing platform Pastebin for distributing malicious payloads, hpingbot’s developers have demonstrated remarkable stealth and efficiency.
Exploiting Pastebin for Payloads
Unlike traditional botnets reliant on static infrastructure, hpingbot uses Pastebin to host and regularly update its payload links.
Hard-coded Pastebin URLs embedded in the malware enable operators to push new configuration files or download scripts, leveraging Pastebin’s anonymity and accessibility.
Since mid-June, researchers observed these Pastebin payloads evolving from simple IP lists to sophisticated download instructions.
Payload delivery now includes install scripts, such as payload.sh, which dynamically identify the system architecture, fetch the correct binary, configure persistence (leveraging Systemd, SysVinit, and Cron), and auto-delete forensic traces demonstrating advanced operational security.
Pastebin’s role as a command-and-control relay not only complicates detection for defenders but also provides attackers with flexible, scalable load distribution.
Additionally, monitoring data indicates rapid version updates and frequent changes to the C&C server, further frustrating traditional tracking mechanisms.
The Role of Hpingbot and Hping3 in DDoS Campaigns
Central to hpingbot’s offensive toolkit is its integration with hping3, the versatile network testing tool favored by both security practitioners and cybercriminals.
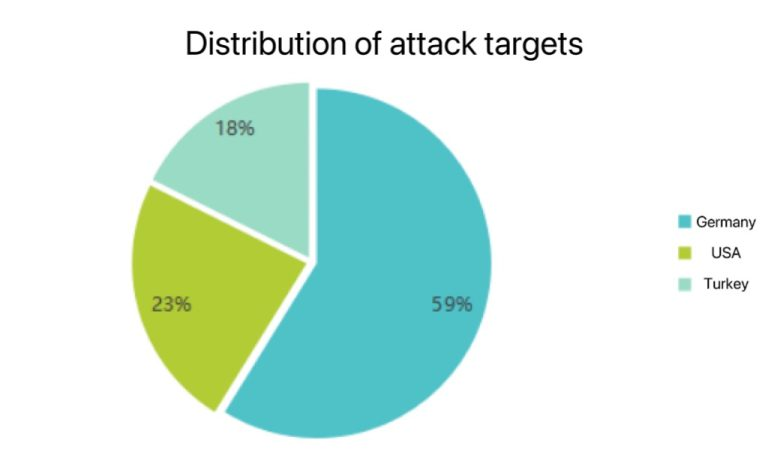
For Linux devices, hpingbot installs hping3 and then issues DDoS instructions in plaintext, targeting countries such as Germany, the US, and Turkey through command-line parameterization.
Supported attack types include SYN, UDP, ACK, mixed-mode floods, and more, all executed via hping3’s customizable packet-generation capabilities.
While the Windows variant of hpingbot cannot leverage hping3 directly, its high activity suggests a dual function: distributing and executing arbitrary payloads.
This provides attackers with a persistent foothold for launching future malware or ransomware, aligning with current trends where botnets serve as multi-purpose outposts for APT and ransomware groups.
The rapid evolution, cross-platform capabilities, and flexible infrastructure of hpingbot signal the rise of a professionalized, well-funded threat group.
Its use of Pastebin, repeated iteration, and the development of specialized payloads and distribution modules highlight its potential for long-term, multi-stage cyber campaigns.
Security teams worldwide are urged to increase vigilance, as Hackingbot’s operators continue to refine and expand their reach.
IOC
45.139.113.61
193.32.162.210
http://128.0.118.18
http://93.123.118.21
http://94.156.181.41
F33E6976E3692CB3E56A4CC9257F5AAE
.png?w=696&resize=696,0&ssl=1)





