A significant data breach that exposes the browsing habits and personal information of users visiting illegal hacking forums.
On Friday, July 18, the team discovered an unsecured Elasticsearch database containing approximately 22 million web request records, with 95% of the traffic directed to Leakzone.net, a prominent dark web forum specializing in distributing hacking tools, exploits, and compromised accounts.
Each record contained sensitive information including domain requests, user IP addresses, geographical locations, and internet service provider details, providing an unprecedented glimpse into the operations of one of the internet’s most active cybercriminal marketplaces.
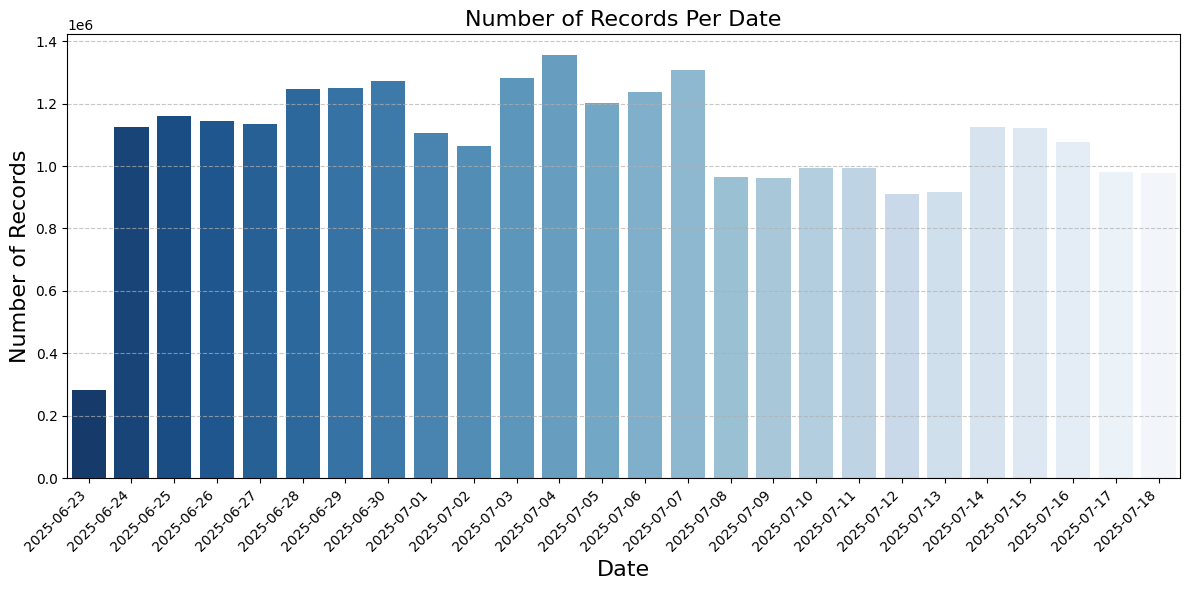
The exposed database contained records spanning from June 25 to the time of discovery, capturing approximately one million daily requests to Leakzone.net with a median request size of 2,862 bytes.
UpGuard researchers confirmed the database’s authenticity by registering an account with Leakzone and observing their own IP address appear in the logs.
The leaked data revealed 185,000 unique IP addresses accessing the forum, significantly exceeding Leakzone’s total user base of 109,000 registered members.
Leakzone represents part of a continuing lineage of illegal forums that emerged after law enforcement shutdowns of similar platforms.
While authorities seized the original Raid Forums in 2022 and arrested the founder of its replacement, Breach Forums, in 2023, Leakzone has maintained operations since gaining traction in late 2020.
The forum serves as a marketplace for illicit cyber materials including stolen credentials, pornography collections, and hacking utilities.
VPN and Proxy Usage
Analysis of the traffic patterns revealed sophisticated privacy measures employed by forum users.
There were about a million requests per day with a median “request_size” of 2862 bytes– numbers indicative of normal traffic to a reasonably successful website.
Approximately 5% of requests originated from public proxies, accounting for 1.3 million records across nearly 4,000 IP addresses.
More significantly, researchers identified clear evidence of widespread VPN usage through traffic distribution analysis.
The data showed unusual clustering around specific IP addresses operated by major service providers, particularly Cogent Communications, which offers VPN services.
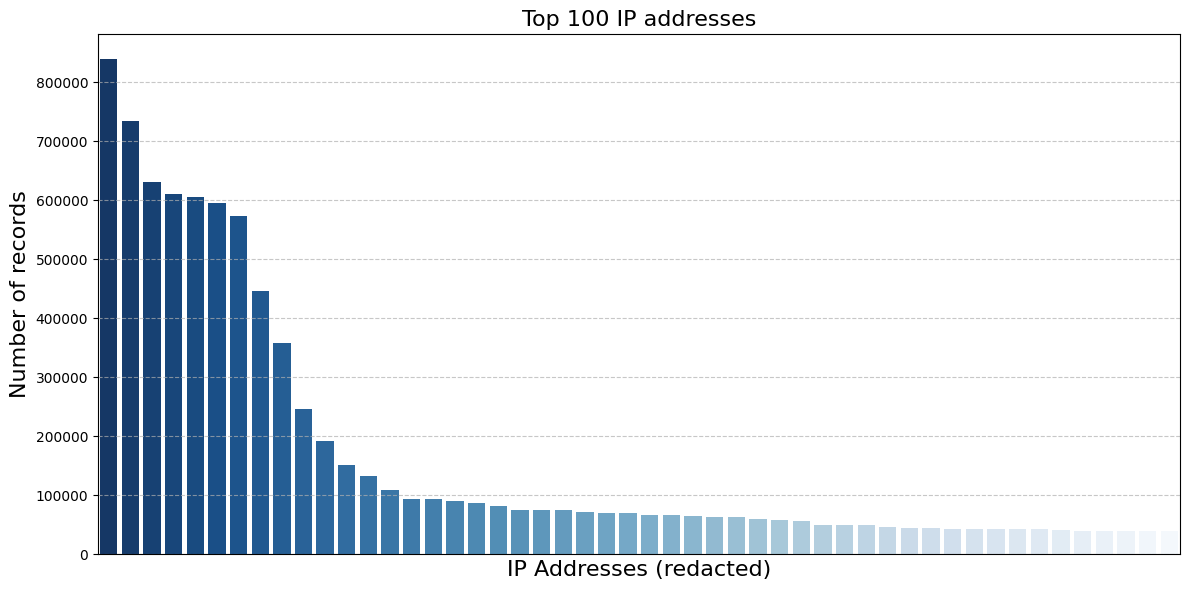
Three Cogent-operated IP addresses ranked among the most active, collectively generating around 600,000 records in a pattern suggesting shared VPN infrastructure.
Additional heavily-trafficked IP addresses traced to Lithuania and the UAE, likely representing VPN exit nodes serving users from different geographical locations.
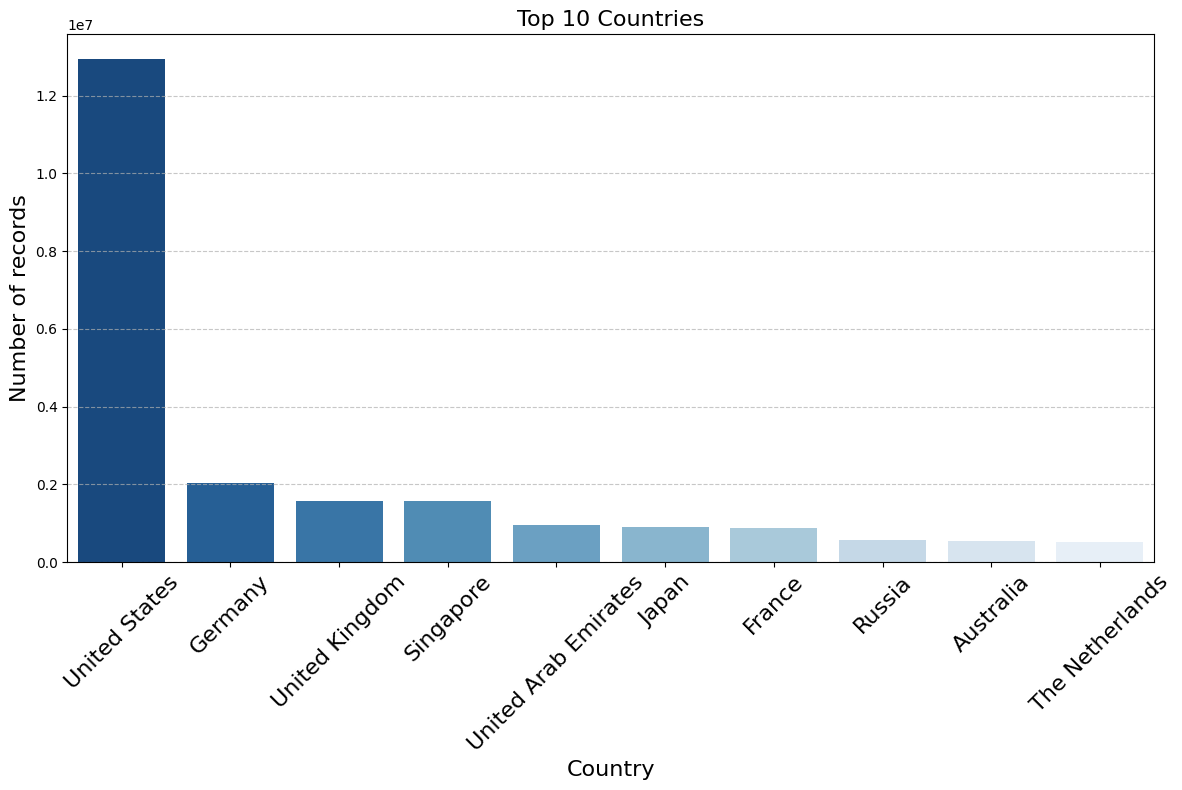
The majority of traffic originated from mainstream cloud providers including Amazon, Microsoft, and Google, with a notable absence of direct Chinese traffic.
Chinese users appeared to route connections through proxy servers in other countries, with Huawei Cloud traffic showing Singapore as the country of origin despite the company’s Chinese headquarters.
Security Implications
The data breach highlights critical privacy vulnerabilities for individuals accessing illegal marketplaces.
Researchers noted that visiting Leakzone doesn’t necessarily indicate malicious intent, as cybersecurity professionals and threat intelligence firms regularly monitor such platforms.
While 39% of IP addresses appeared only once in the logs, potentially representing direct connections without privacy protection, the concentration of traffic through specific VPN providers creates new tracking opportunities for law enforcement.
However, the exposure demonstrates how digital anonymity remains fragile, particularly following recent arrests including the suspected administrator of the XSS.is hacking forum in Ukraine.
The incident underscores the ongoing challenge of maintaining privacy in digital spaces, even when users employ sophisticated anonymization techniques, as browsing activity linked to IP addresses remains vulnerable to unexpected data exposures.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




