Cybersecurity researchers at FortiGuard Labs have disclosed a new ransomware threat identified as Dark 101, delivered as an obfuscated .NET binary.
This advanced malware, now categorized under the Dark 101 malware family, follows a calculated multistage attack sequence that disables system recovery capabilities and encrypts user data before extorting victims for ransom in Bitcoin.
The ransomware is designed to bypass traditional detections, initiating its attack by checking for signs of analysis.
If it detects that the executable is not running from the %Appdata% directory, it delays execution by 10 seconds a simple yet effective sandbox evasion technique.
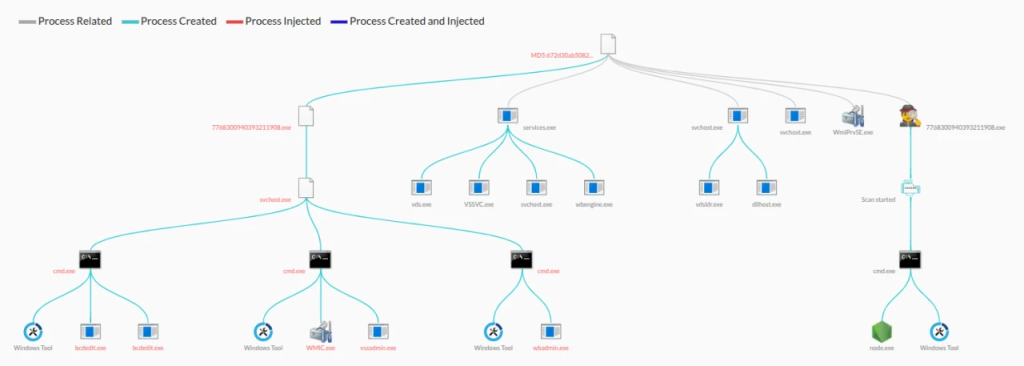
Once past the environment check, it self-replicates as svchost.exe in %Appdata%, mimicking the legitimate Windows process to appear benign, while its suspicious location red-flags the process for behavioral detection systems like FortiSandbox.
Disabling Recovery Options and Task Manager
A key highlight of the Dark 101 ransomware is its anti-recovery mechanism. It executes a set of destructive system commands designed to make file restoration nearly impossible. These include:
vssadmin delete shadows /all /quiet– to eliminate Volume Shadow Copieswmic shadowcopy delete– to further erase shadow copies via Windows Management Instrumentationwbadmin delete catalog –quiet– to delete Windows Backup Catalogs
By executing these commands in succession, the malware ensures users cannot restore their systems using built-in Windows recovery tools.
To enhance its persistence and minimize user intervention, Dark 101 modifies the Windows Registry at:
textHKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System\DisableTaskMgr
Setting the DisableTaskMgr Disabling Task Manager to 1 effectively renders it useless, leaving users without a crucial tool to detect or terminate malicious activity.
Targeted Encryption and Ransom Demand
Once system defenses are neutralized, the ransomware scans user-accessible directories for files matching specific extensions associated with image, document, archive, database, and other types of personal data.
Matched files are encrypted and renamed with a random four-character extension. Alongside the encrypted files, a ransom note read_it.txt is dropped in each affected directory.
The note demands payment in Bitcoin and typically includes contact information for negotiating decryption.
Fortinet Response and Protection
Fortinet has classified the threat under MSIL/Kryptik.SAC!tr. Ransom confirms that its security solutions, including FortiGate, FortiEDR, and FortiClient, can detect and block the malware.
Organizations are urged to maintain up-to-date AV signatures and review suspicious registry and command-line activity.
MD5 hash of known sample: ae3dd3d1eedb6835e6746d51d9ab21c6.
Fortinet also recommends its free NSE 1 training on information security awareness to help users stay alert against evolving cyber threats.
IOCs
MD5sum:
ae3dd3d1eedb6835e6746d51d9ab21c6
.jpg?w=696&resize=696,0&ssl=1)





