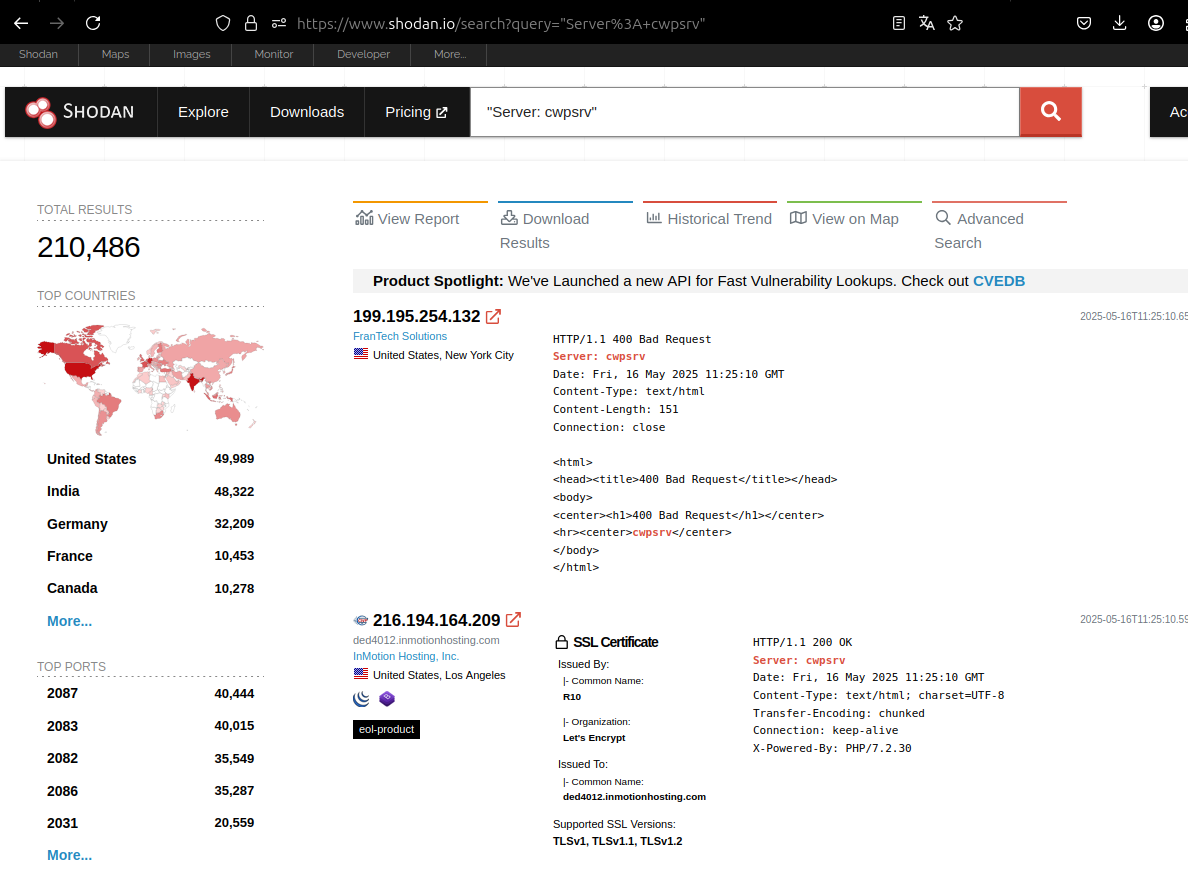
A severe security vulnerability has been discovered in CentOS Web Panel (CWP), a widely-used free web hosting control panel that manages over 200,000 server instances worldwide.
The vulnerability, designated as CVE-2025-48703, allows unauthenticated attackers to execute arbitrary commands remotely on affected servers, posing a significant threat to web hosting infrastructure globally.
CentOS Web Panel, first introduced in 2013 as a free alternative to commercial solutions like cPanel and Plesk, provides administrators with tools to manage essential server services including Apache/NGINX web servers, MySQL/MariaDB databases, email systems, and DNS configurations.
The platform’s widespread adoption makes this vulnerability particularly concerning for the web hosting community.
The security vulnerability stems from improper authentication verification in the user panel’s file management feature, specifically in the file permissions change functionality.
Researchers discovered that the application fails to properly validate user credentials when processing requests to modify file permissions, allowing attackers to bypass authentication entirely by manipulating HTTP requests.
Linux CentOS Web Panel Vulnerability
The vulnerability combines two critical security issues: an authentication bypass and command injection.
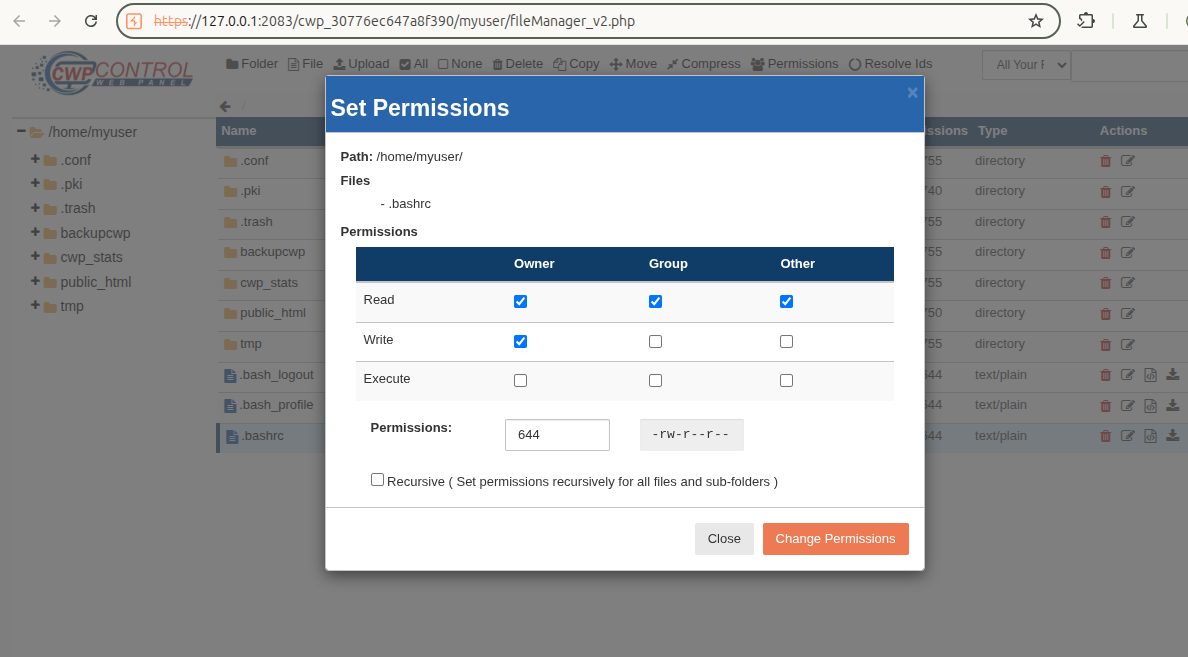
The first component allows attackers to send requests without proper user authentication by removing user identifiers from URLs while still having the server process the requests normally.
This bypasses the intended security controls that should restrict access to authenticated users only.
The second component involves a command injection vulnerability in the ‘t_total’ parameter, which handles file permission modes in the chmod system command.
Due to insufficient input sanitization, attackers can inject arbitrary commands through this parameter, leading to remote code execution on the target server.
The source code of CWP is protected by ionCube . IonCube is a PHP encryption and licensing tool designed to secure and optimize PHP-based applications.
Security researchers demonstrated the exploit using a simple curl command that leverages both vulnerabilities simultaneously.
The attack requires knowledge of a valid non-root username on the target CWP instance, but no authentication credentials are needed.
Once exploited, attackers gain shell access with the privileges of the targeted user account, potentially allowing further system compromise.
The vulnerability affects CWP versions 0.9.8.1204 and 0.9.8.1188, which were tested on CentOS 7 systems.
Given that CWP instances can be easily identified using search engines like Shodan.io with the search pattern “Server: cwpsrv,” the attack surface is substantial and easily discoverable by malicious actors.
PoC Code Circulates
Following responsible disclosure practices, the vulnerability was reported to CWP developers on May 13, 2025, and assigned CVE-2025-48703 ten days later.
The development team responded promptly, releasing a patch in version 0.9.8.1205 during June 2025, approximately one month after the initial report.
However, the recent public released proof-of-concept exploit code on security research platforms has heightened the urgency for system administrators to apply available patches immediately.
The working exploit demonstrates how attackers can establish reverse shell connections to compromised servers, providing complete command-line access to the underlying system.
System administrators running CentOS Web Panel installations should immediately update to version 0.9.8.1205 or later to remediate this critical vulnerability.
Organizations unable to update immediately should implement network-level protections and closely monitor CWP instances for suspicious activity until patches can be applied.
The discovery highlights the ongoing security challenges faced by web hosting control panels and underscores the importance of regular security assessments for widely-deployed server management software.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




