A critical security vulnerability in Base44, a popular AI-powered “vibe coding” platform recently acquired by Wix, that allowed unauthorized access to private applications built by users.
The vulnerability, which has since been patched, could have exposed sensitive enterprise data including internal chatbots, HR operations, and business tools to unauthorized attackers.
The vulnerability was remarkably straightforward to exploit, requiring only a non-secret app_id value to access undocumented registration and email verification endpoints.
By providing this publicly visible identifier, attackers could create verified accounts for private applications, effectively bypassing all authentication controls including Single Sign-On (SSO) protections.
Wiz Research discovered the vulnerability through reconnaissance of Base44’s publicly accessible domains, identifying exposed Swagger-UI interfaces that revealed internal API documentation.
The researchers found that the api/apps/{app_id}/auth/register and api/apps/{app_id}/auth/verify-otp endpoints were accessible without authentication, allowing anyone to register for private applications.
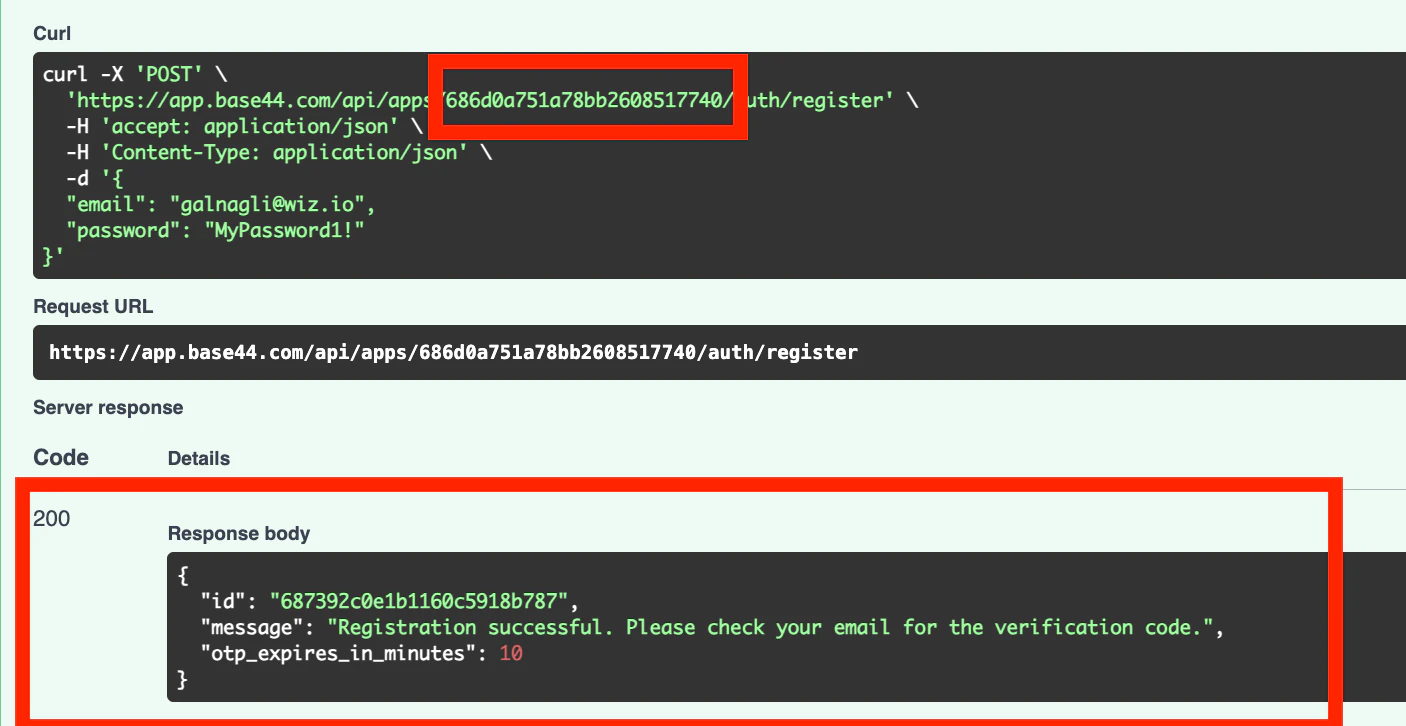
The app_id values, which appeared as random strings, were not actually secret and could be easily obtained from any Base44 application’s URI and manifest.json file path.
This meant that attackers could systematically compromise multiple applications across the platform with minimal technical sophistication.
AI Vibe Coding Platform Vulnerability
The vulnerability posed significant risks to enterprises using Base44 for critical business functions.
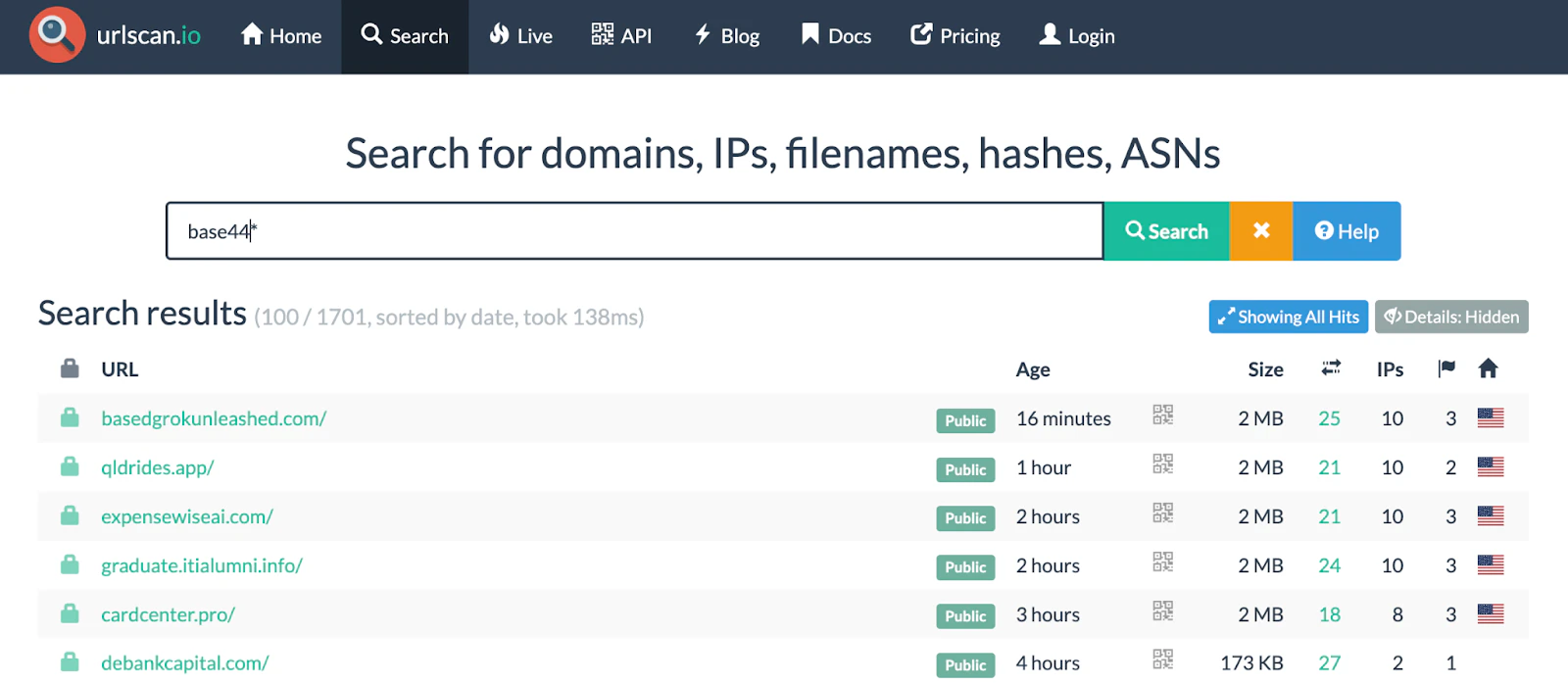
We used platforms such as urlscan that helped us discover additional applications empowered by the vibe coding platform by searching for HTML data.
During their research, Wiz confirmed that authentication bypass was possible across several enterprise applications handling sensitive data including internal chatbots, knowledge bases, and PII operations.
The shared-risk model of vibe coding platforms amplified the vulnerability’s impact, as all applications run on the vendor’s shared infrastructure, meaning every customer inherits the vendor’s security posture.
This creates a critical single point of failure where a single vulnerability in the platform’s core components can instantly jeopardize every application built upon it.
The rapid enterprise adoption of these platforms for handling sensitive data through internal chatbots, automations, and business tools made this vulnerability particularly concerning.
The researchers used two methods to identify vulnerable applications: enterprise applications with custom domains and general reconnaissance techniques.
Broader Industry Implications
Following responsible disclosure on July 9th, 2025, Wix implemented a fix within 24 hours that properly validates application privacy settings before allowing user registration.
Wix conducted a thorough investigation and confirmed there was no evidence of past abuse or compromise across the Base44 user base during the vulnerable period.
This incident highlights critical gaps in evaluating AI development platforms, where security discussions often focus on AI-specific threats while overlooking fundamental security controls like proper authentication and secure API design.
The vulnerability demonstrates how vibe coding platforms create new attack surfaces that traditional security frameworks may not adequately address.
The security community, vendors, and organizations must work together to build robust security foundations as these transformative platforms continue to evolve and gain enterprise adoption.
Through responsible disclosure and open dialogue, the industry can help strengthen security postures and develop with security as a core consideration.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




