Cybersecurity researchers from Zscaler ThreatLabz, in collaboration with TibCERT, have uncovered two sophisticated cyberattack campaigns targeting the Tibetan community in anticipation of the Dalai Lama’s 90th birthday in July 2025.
The campaigns, dubbed Operation GhostChat and Operation PhantomPrayers, deployed advanced malware including Ghost RAT and PhantomNet backdoors through multi-stage infection chains that exploited legitimate software vulnerabilities.
Strategic Web Compromises and Social Engineering Tactics
The threat actors capitalized on heightened online activity surrounding the Dalai Lama’s milestone birthday by compromising legitimate websites and creating convincing replicas.
In Operation GhostChat, attackers replaced a legitimate link on tibetfund.org with a malicious redirect to thedalailama90.niccenter[.]net, which closely mimicked the original site.
The fake webpage offered a backdoored version of Element, a popular encrypted messaging application, hosted at theelement. niccenter[.]net.
Operation PhantomPrayers employed a different approach, using the subdomain hhthedalailama90.niccenter[.]net to distribute malicious software masquerading as “special prayer check-in” software.
The application, built with PyQT5 and packaged using PyInstaller, displayed an interactive map showing fabricated check-ins from users worldwide to enhance the social engineering deception.
Advanced Multi-Stage Attack Methodology
Both campaigns utilized sophisticated DLL sideloading techniques to bypass security measures.
In Operation GhostChat, the legitimate Element.exe application was configured to automatically load a malicious ffmpeg.dll file, which served as the initial stage loader.
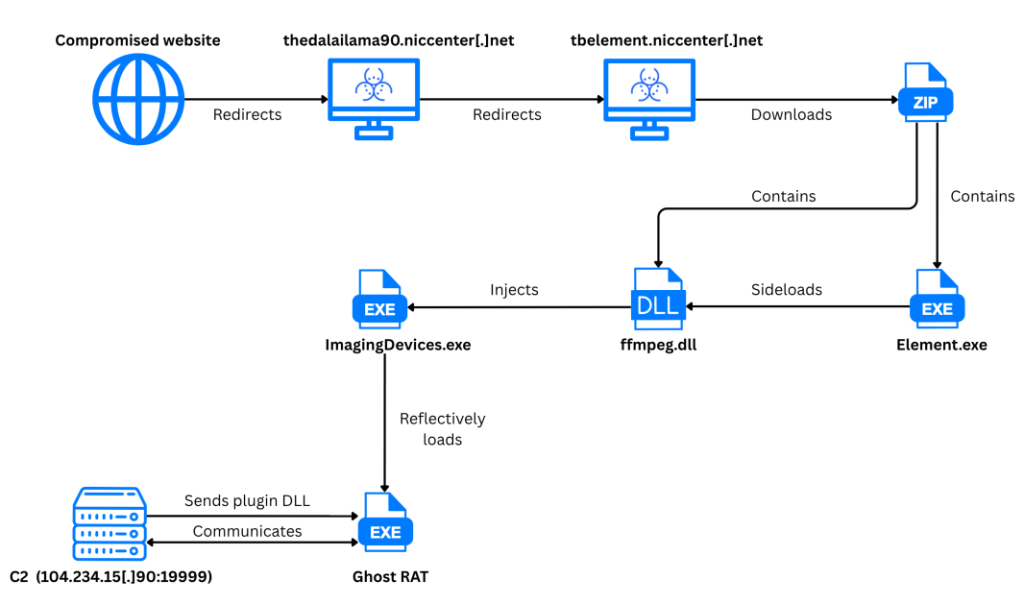
The attack employed several evasion techniques, including mapping a fresh copy of ntdll.dll from disk to bypass API hooks and utilizing low-level Windows APIs, such as NtCreateSection and RtlCreateUserProcess, for code injection.
The malware demonstrated advanced persistence mechanisms, creating registry entries under HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run and utilizing a shared memory section-based code injection technique to inject shellcode into legitimate Windows processes, such as ImagingDevices.exe.
The final payloads included Ghost RAT, which communicated with command-and-control servers at 104.234.15[.]90:19999 using a custom “KuGou” packet header, and PhantomNet backdoor connecting to 45.154.12[.]93:2233.
Attribution and Implications
Researchers attribute these campaigns with high confidence to China-nexus APT groups based on the victimology targeting the Tibetan community, the specific malware variants used, and the deployment of tailored tactics, techniques, and procedures (TTPs).
Both Ghost RAT and PhantomNet have been previously associated with Chinese state-sponsored cyber espionage operations, with PhantomNet linked to the TA428 APT group.
The campaigns highlight the continued targeting of politically sensitive communities through sophisticated technical means combined with culturally relevant social engineering tactics.
Indicators of Compromise (IOCs)
File indicators
| MD5 hash | SHA1 hash | SHA256 hash | Filename | Description |
|---|---|---|---|---|
| 42d83a46250f788eef80ff090d9d6c87 | ff9fddb016ec8062180c77297d478b26d65a7a40 | 0ad4835662b485f3a1d0702f945f1a3cf17e0a5d75579bea165c19afd1f8ea00 | TBElement.zip | Malicious ZIP archive |
| 5b63a01a0b3f6e06dd67b42ad4f18266 | 71f09721792d3a4f1ea61d1f3664e5a503c447b2 | d896953447088e5dc9e4b7b5e9fb82bcb8eb7d4f6f0315b5874b6d4b0484bd69 | Element.exe | Legitimate executables vulnerable to DLL sideloading. |






