A critical analysis of recent attack simulations reveals how misconfigured Azure environments allow threat actors to escalate from anonymous access to full control of cloud infrastructure.
Security researchers at Improsec documented an attack path exploiting common Azure misconfigurations, demonstrating how attackers can compromise credentials, escalate privileges, and eventually gain Global Administrator rights.
This end-to-end compromise chain highlights systemic security gaps affecting organizations using Microsoft’s cloud platform.
The attack begins with unauthenticated attackers scanning Azure subdomains using tools like MicroBurst to identify publicly accessible storage accounts.
Researchers found that exposed blob containers containing credential files (like test.csv with username/password combinations) provide initial access vectors.
Once credentials are harvested, attackers bypass multi-factor authentication checks using MFASweep to verify unprotected accounts.
Compromised low-privilege accounts then enable reconnaissance of Azure Active Directory (Azure AD). Attackers specifically target dynamic security groups with privileged role assignments.
By inviting guest users with names matching dynamic group rules (e.g., “automationadmin”), attackers inherit group permissions like “Automation Contributor” roles.
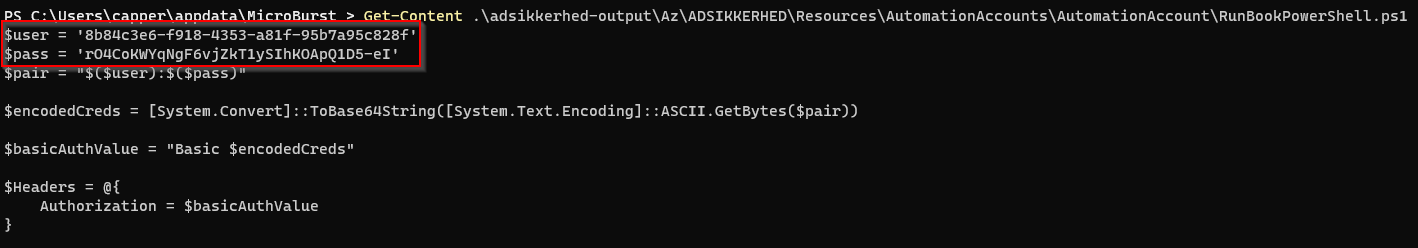
This access allows dumping Automation Account runbooks, often containing hardcoded service principal credentials with elevated privileges.
Privilege Escalation Techniques
With “Virtual Machine Contributor” access, attackers execute commands on Azure VMs to extract managed identity tokens.

These tokens grant access to linked resources like Key Vaults, where credentials for higher-privileged users (e.g., “AppOwner”) are stored.
Researchers demonstrated token extraction via Azure Instance Metadata Service (IMDS) endpoints, yielding keys to sensitive data stores.
Ownership of application registrations becomes critical at this stage. Attackers add new credentials to compromised service principals assigned powerful roles like “Storage Account Contributor” at the management group level.
This provides write access to cloud storage, including Cloud Shell profiles.

By poisoning Cloud Shell image files with malicious PowerShell profiles, attackers inject privilege escalation commands that trigger when legitimate users launch terminals.
Mitigations
According to Report, Security teams should enable Azure Defender for Resource Manager to detect reconnaissance tools and configure Conditional Access policies requiring compliant devices for Azure management.
When victims launch the poisoned Cloud Shell, it silently grants attackers Global Administrator rights in Azure AD. From this position, attackers self-assign “User Access Administrator” roles, achieving full infrastructure control.
To prevent such attacks, researchers recommend:
- Hardening storage configurations: Disabling public blob access, enforcing secure transfer, and rotating access keys every 90 days.
- Securing identities: Enforcing MFA universally, restricting guest invitations, and avoiding dynamic groups for privileged roles.
- Monitoring critical activities: Alerting on VM RunCommand executions, service principal credential changes, and Global Administrator role assignments.
- Implementing least privilege: Scoping permissions to resource groups instead of subscriptions and using Managed Identities instead of hardcoded credentials.
Regular audits of external identities and access reviews are equally critical in multi-tenant environments.
The endgame involves internal phishing targeting privileged administrators. Attackers send specially crafted Cloud Shell links to administrators via Teams.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




