Since 2018, the advanced persistent threat group known as APT-C-36, or Blind Eagle, has been waging a relentless cyber assault campaign targeting organizations across Latin America, with a particular focus on Colombia.
The group’s operations have consistently threatened government institutions, financial organizations, and critical infrastructure sectors whose disruption can have wide-reaching societal and economic impacts.
Recent intelligence reveals that Blind Eagle’s modus operandi remains consistent: spear-phishing emails serve as the initial vector, delivering malicious links or attachments to targeted employees.
Once a recipient interacts with the payload, the attackers exploit vulnerabilities such as CVE-2024-43451—a now-patched Microsoft Windows flaw that once allowed unauthorized access to NTLMv2 password hashes.
While Microsoft addressed this vulnerability in November 2024, Blind Eagle continues to leverage the minimal user interaction required to trigger malicious downloads, adapting tactics to maintain operational effectiveness.
Technical Execution and Detection
The attack chain observed in recent campaigns is sophisticated. Victims receive phishing emails containing a malicious link; clicking the link initiates a WebDAV request over HTTP port 80, using the user agent ‘Microsoft-WebDAV-MiniRedir/10.0.19044’.
WebDAV, a protocol for remote file access, enables attackers to deliver and execute malware on compromised devices.
Subsequent payloads are downloaded via additional WebDAV requests, with attackers receiving notifications whenever a recipient downloads a malicious file a clear indicator of a successful compromise.
Darktrace, a leading AI-driven cybersecurity firm, detected Blind Eagle activity on a Colombian customer’s network in late February 2025.
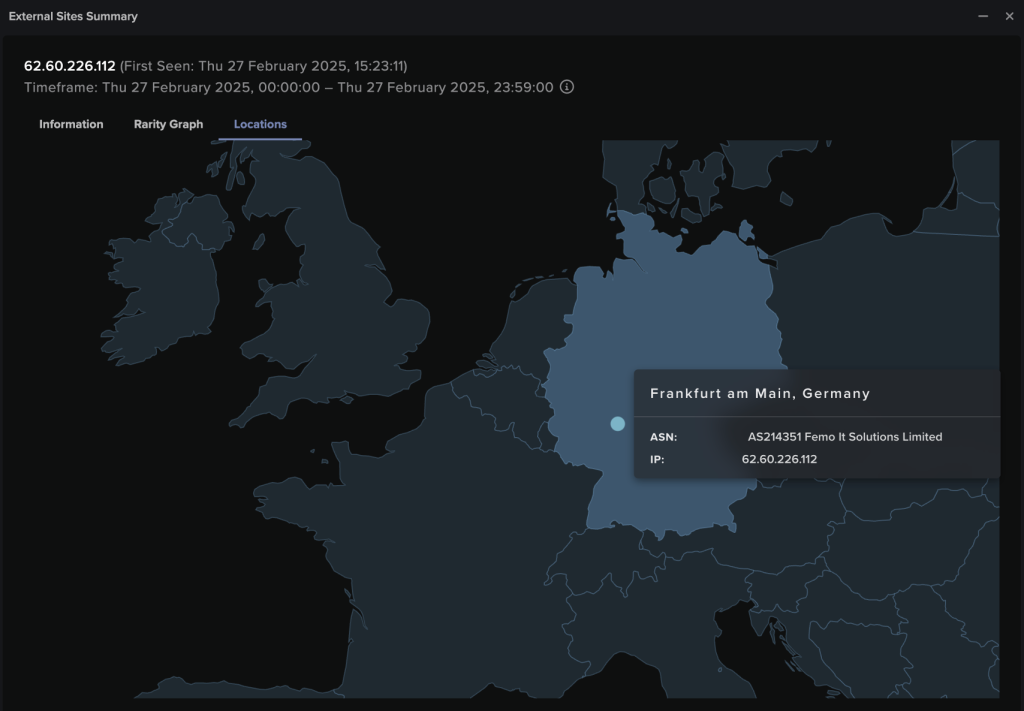
Over just five hours, a device was redirected to a rare external IP (62.60.226.112) located in Germany, an endpoint linked to phishing and malware campaigns by multiple open-source intelligence providers.
The device downloaded an executable file (http://62.60.226.112/file/3601_2042.exe) and then connected to a dynamic DNS endpoint (21ene.ip-ddns.com), a standard method used by threat actors to maintain persistent access despite changing IP addresses.
Further investigation revealed associations with Remcos malware, a remote access trojan (RAT) frequently distributed via phishing.
The compromised device proceeded to make unusual connections to additional endpoints, including diciembrenotasenclub.longmusic.com on TCP port 1512, and uploaded significant data volumes (60 MiB and 5.6 MiB, respectively).
This activity triggered multiple high-priority alerts in Darktrace’s Enhanced Monitoring models, indicating indicators of compromise (IoCs) such as anomalous file downloads, suspicious external data transfers, and beaconing to known malicious domains.
Mitigation and Future Outlook
The incident highlights the need for proactive, anomaly-based detection and autonomous response capabilities.
While timely patch management is essential, it is not sufficient to counter threat actors like Blind Eagle, who rapidly adapt their tactics.
Organizations must invest in advanced security solutions that can identify deviations in user or device behavior and respond autonomously to contain threats.
In summary, APT-C-36 (Blind Eagle) represents a persistent and evolving cyber threat to Latin America’s most critical sectors.
Their ability to exploit vulnerabilities, maintain persistence, and exfiltrate data highlights the urgent need for robust, adaptive cybersecurity defenses that combine anomaly detection with autonomous response to safeguard against sophisticated adversaries.
IoCs
IoC – Type – Confidence
Microsoft-WebDAV-MiniRedir/10.0.19045 – User Agent
62[.]60[.]226[.]112 – IP – Medium Confidence
hxxp://62[.]60[.]226[.]112/file/3601_2042.exe – Payload Download – Medium Confidence
21ene.ip-ddns[.]com – Dynamic DNS Endpoint – Medium Confidence
diciembrenotasenclub[.]longmusic[.]com – Hostname – Medium Confidence
.webp?w=696&resize=696,0&ssl=1)





