A two high-severity vulnerabilities in Anthropic’s Model Context Protocol (MCP) Filesystem Server that allow attackers to escape security sandboxes and execute arbitrary code on host systems.
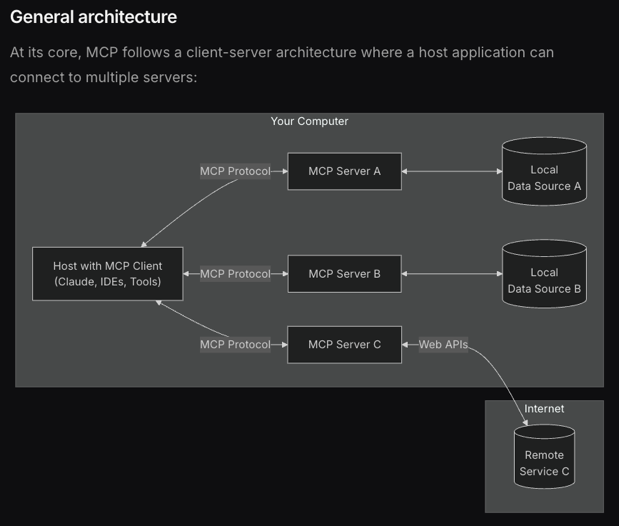
The findings come as MCP gains rapid adoption as a framework enabling large language models like Claude Desktop to interact with external data sources and services.
The research team identified two distinct vulnerabilities that fundamentally compromise the Filesystem MCP Server’s security boundaries.
The first vulnerability, designated CVE-2025-53110 with a CVSS score of 7.3, exploits a directory containment bypass through naive prefix matching.
This flaw allows attackers to access directories outside the intended sandbox by crafting paths that begin with approved directory names but extend beyond their scope.
The second and more severe vulnerability, CVE-2025-53109 with a CVSS score of 8.4, leverages symbolic links to completely bypass access controls.
Attackers can create symbolic links pointing to any location on the filesystem, including critical system files like /etc/sudoers.
Due to poor error handling in the server’s validation logic, the symlink bypass mechanism fails to properly restrict access, allowing unauthorized file operations across the entire system.
The Filesystem MCP Server by Anthropic, for example, handles file reads and writes, restricting the AI to a predefined “allowed directory” in a JSON config. It’s meant to keep the AI’s new limbs safely sandboxed.
“The vulnerabilities affect the core security model of the Filesystem MCP Server,” explained the Cymulate researchers.
“An attacker can leverage legitimate MCP Server functionality to read or write anywhere on disk and trigger code execution – all without exploiting traditional memory corruption bugs or dropping external binaries.”
Anthropic MCP Server Vulnerabilities
The attack scenarios demonstrate how these vulnerabilities can be chained together for maximum impact.
Attackers first exploit the directory containment bypass to create malicious directories that share prefixes with allowed paths.
The vulnerability lies in how the server checks file paths: it uses a naive string prefix match, essentially a ‘startswith’ check to verify if a requested path falls within an allowed directory, like “/private/tmp/allow_dir”.

They then use symbolic links within these directories to point to sensitive system files or locations where they can plant malicious code.
The research team demonstrated a particularly concerning attack vector involving macOS Launch Agents.
By writing malicious property list files to the user’s LaunchAgents directory, attackers can achieve persistent code execution that triggers automatically when users log in.
This technique allows the malicious code to execute with the privileges of the MCP server process, potentially leading to full system compromise if the server runs with elevated permissions.
“Because LLM workflows often run with elevated user privileges for convenience, successful exploitation can translate directly into root-level compromise,” the researchers noted.

The vulnerabilities are especially dangerous in enterprise environments where MCP servers might operate with administrative privileges to access various system resources.
Mitigations
Anthropic responded quickly to the vulnerability disclosure, which followed a responsible disclosure timeline.
The vulnerabilities were discovered and reported on March 30, 2025, acknowledged by Anthropic on May 1, and patched on July 1, 2025.
The company has released security updates addressing both vulnerabilities in npm package version 2025.7.1, with all versions prior to 0.6.3 and 2025.7.1 considered vulnerable.
The research team praised Anthropic’s security and engineering teams for their “fast, professional handling” of the disclosure process.
Early adoption metrics show a high uptake of the patched version following its release, significantly reducing the attack surface across the MCP ecosystem.
Security experts recommend immediate updates to the latest patched release and implementing the principle of least privilege for all MCP deployments.
Organizations should also validate their security posture against these attack vectors, as the vulnerabilities highlight broader risks in AI-driven system integrations where language models interact with external resources.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




