A major security vulnerability in the Android stalkerware service Catwatchful has exposed the plaintext login credentials of over 62,000 users, revealing the extensive reach of consumer spyware applications.
The breach, discovered through a SQL injection vulnerability, highlights ongoing security concerns surrounding commercially available surveillance software that operates in legal gray areas while potentially enabling domestic abuse and harassment.
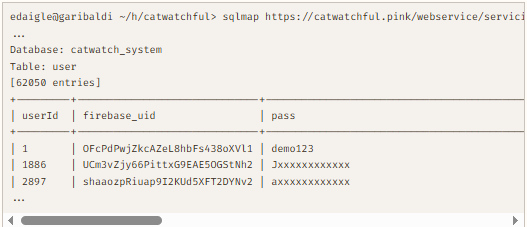
The vulnerability was discovered by security researcher Eric Daigle in June 2025 during routine analysis of known stalkerware services.
Daigle found that Catwatchful’s backend server contained a critical SQL injection vulnerability that allowed unauthorized access to the entire user database without authentication.

The vulnerability existed in the service’s API endpoint used to retrieve device information, enabling attackers to extract sensitive data using standard penetration testing tools.
The exposed database contained comprehensive account information for approximately 62,050 users, including email addresses, passwords stored in plaintext format, Firebase user identifiers, account creation dates, and last access timestamps.
This represents one of the largest known breaches of stalkerware user data, providing unprecedented insight into the scale of commercial surveillance software adoption.
Sophisticated Spyware Operations
Catwatchful marketed itself as a comprehensive Android monitoring solution, boldly advertising its ability to operate covertly on target devices.
The service’s website featured explicit messaging about invisible monitoring capabilities, stating that the app “cannot be detected, cannot be uninstalled, cannot be stopped, cannot be closed.”
The application disguised itself with a generic “Settings” icon while requesting extensive system permissions to monitor calls, messages, location data, and even capture live photos and audio recordings.
The live photo and microphone options are particularly creepy, successfully taking a photo or recording and uploading it for me to view near-instantly on the control panel without giving the phone user the slightest sign that anything is amiss.
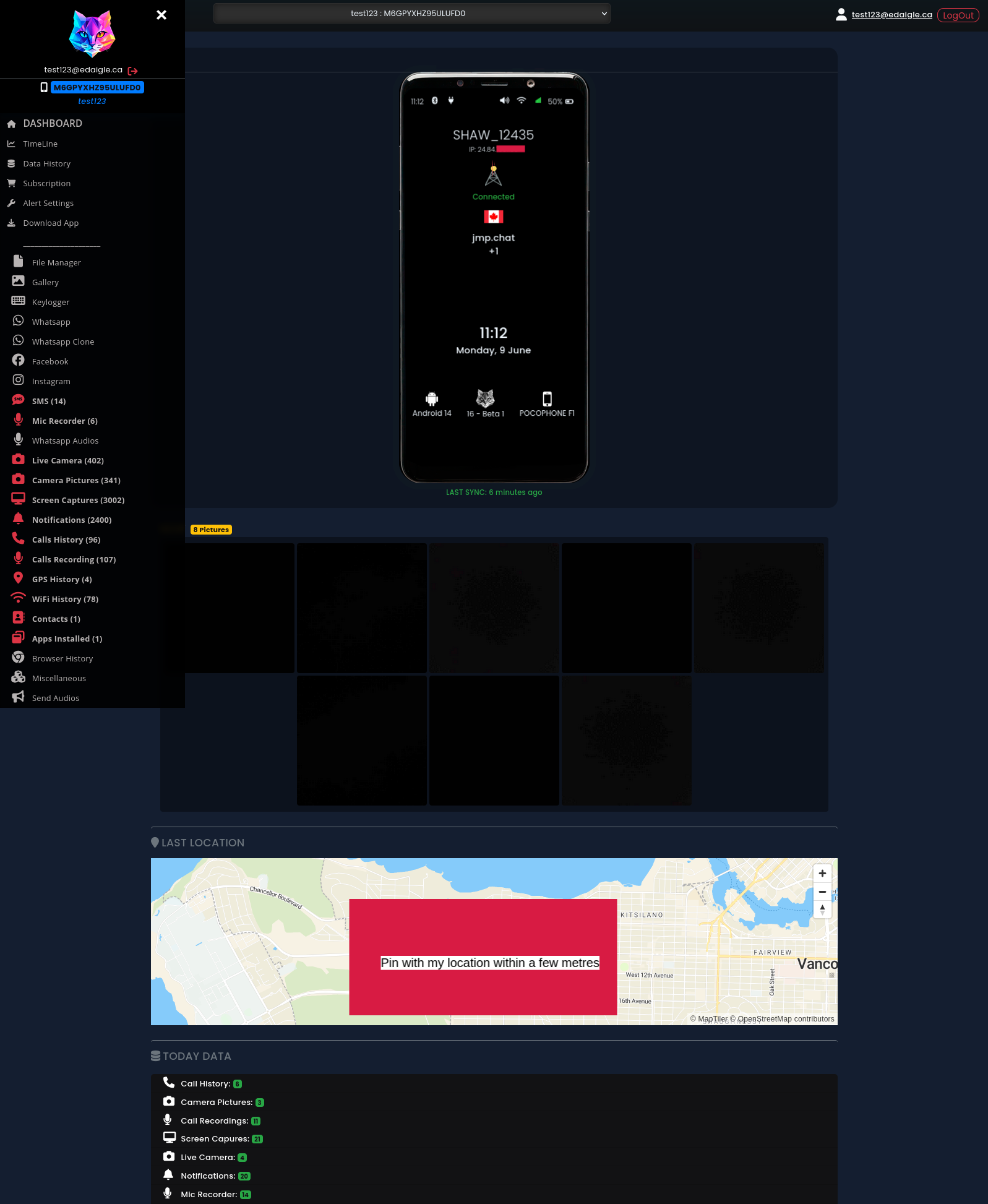
Unlike many stalkerware services that rely on white-label solutions, Catwatchful appeared to operate as an independent service with sophisticated technical infrastructure.
The application utilized Google Firebase for data storage and Firebase Cloud Messaging for command delivery, while maintaining a separate PHP-based API server for account management.
Testing revealed that the surveillance features functioned reliably with minimal latency, distinguishing it from many poorly-constructed competing services.
Remediation Timeline
Following the discovery, journalist Zack Whittaker coordinated disclosure efforts with major technology companies and hosting providers.
Google was notified on June 23, 2025, and subsequently flagged the service in Safe Browsing while the Firebase team initiated an investigation.
Hosting provider Hosting.com was contacted on June 25, resulting in the temporary shutdown of the primary server infrastructure.
The service operators attempted to maintain operations by migrating to alternative hosting at xng.vju.temporary.site, but this remained vulnerable to the same SQL injection attack.
By June 27, a web application firewall was deployed to block the specific vulnerability, though this represented a reactive rather than comprehensive security improvement.
The incident underscores ongoing challenges in regulating commercially available surveillance software that straddles the line between legitimate parental control applications and tools enabling stalking and domestic abuse.
Despite industry efforts to combat stalkerware, the proliferation of such services continues to pose significant privacy and security risks to potential victims while exposing users’ own sensitive data to security breaches.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




