A critical vulnerability has been identified in ISPConfig, a popular web hosting control panel widely used for managing multiple websites on a single server.
The security flaw found in version 3.2.12p1—exposes systems to privilege escalation risks and arbitrary PHP code execution. Independent researchers collaborating with SSD Secure Disclosure published a detailed analysis, revealing how attackers can manipulate user creation and language modification features to compromise ISPConfig instances.
Technical Analysis: Exploiting Design Flaws
The vulnerability leverages two intertwined design flaws in ISPConfig’s administrative logic:
1. Privilege Escalation via User Management
ISPConfig’s user creation and editing logic contains inadequate validation checks, allowing an authenticated client (with standard user privileges) to escalate to admin and ultimately superadmin status. The control panel supports several user roles, including:
- Client: Basic end user, limited to assigned resources.
- Reseller: Can manage clients but not system settings.
- Remote User: Authenticated via API for specific tasks.
The Flaw:
Remote users with “Client Functions” enabled can execute the client_add function, even with elevated privileges. While there are some permission checks, the system fails to properly validate the types of modules and roles assigned to new users.
Key Code Weakness – User Creation Logic:
php// snippet from klientadd function
protected function klientadd($formdef_file, $reseller_id, $params) {
global $app;
$app->remoting_lib->loadFormDef($formdef_file);
$app->remoting_lib->loadUserProfile($reseller_id);
$sql = $app->remoting_lib->getSQL($params, 'INSERT', 0);
// ... more DB operations ...
$app->remoting_lib->ispconfig_sysuser_add($params, $insert_id);
// ... group and reseller assignments ...
return $insert_id;
}
The crucial missing check: No proper validation on whether a client user can be assigned the admin module.
This allows a remote user to create a client with admin access, then use that account to create an admin user by manipulating HTTP parameters.
Bypassing Role Validation:
ISPConfig attempts to prevent non-superadmin users from creating admin users by checking if typ == 'admin'. However, by crafting a request with, for example, typ empty and typ[1]='admin', this check is bypassed.
Request Example:
textPOST /admin/users_edit.php HTTP/2
Host: ispconfig.example.com:8080
Content-Type: application/x-www-form-urlencoded
username=adminuser&passwort=password123&repeat_password=password123&typ%5B%5D=&typ[]=admin&active=1
Once an admin user is created, the attacker can modify the superadmin user (with ID 1), effectively gaining full control.
2. Arbitrary PHP Code Injection via Language Editor
After elevating to superadmin, attackers can exploit a second vulnerability in the language modification feature. Language files (.lng) are PHP files, so editing them allows direct code execution if input is not properly sanitized.
The Language Editor Vulnerability:
The code responsible for saving language files applies a flawed regex to escape double quotes, aiming to prevent code injection:
php$val = preg_replace('/(^|[^\\\\])((\\\\\\\\)*)"/', '$1$2\\"', $val);
However, this regex can be bypassed by submitting consecutive quotes. Here’s why:
- The pattern: Only matches a ” if it’s at the start or after a non-backslash.
- Problem: If a string contains
"", the first ” is matched, escaped, and the position is consumed. - Result: The second ” is not escaped, allowing for code injection if the value ends in
"";phpinfo();//.
Proof of Concept:
A malicious language update might look like this:
textrecords[error_user_password_incorrect]=Username+or+Password+wrong.""%3Bphpinfo()%3B%2F%2F
When this is saved, the resulting .lng file can include arbitrary PHP code, leading to code execution.
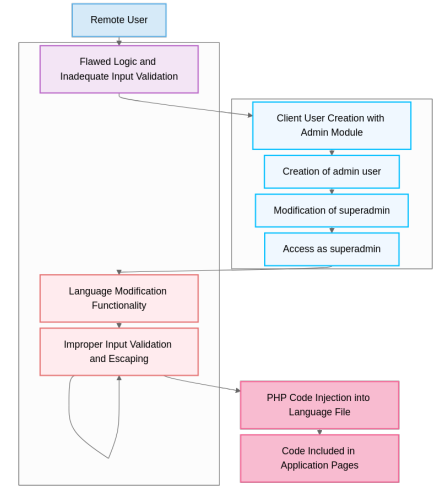
Example Attack Chain:
- Remote user creates a client with admin module.
- Client user creates an admin, bypass checks with crafted request.
- Admin user modifies superadmin (ID 1), gains full control.
- Superadmin injects PHP code via language editor, leading to arbitrary code execution as the web server’s user.
Mitigation Advice and Vendor Response
Vendor Response:
The vendor argued that exploiting these vulnerabilities requires an admin or remote user with elevated privileges, which are not granted to standard users. However, the researchers countered that companies often grant admin or remote privileges, making this a realistic threat.
Mitigation:
- Restrict remote user privileges: Only assign the minimum necessary permissions.
- Update ISPConfig: Monitor for patches and apply them promptly.
- Implement additional input validation: Ensure all user-affected fields are properly sanitized.
- Restrict file write permissions: Limit the ability to write to critical directories.
Summary Table: Attack Flow
| Step | Description | Privileges Needed |
|---|---|---|
| 1 | Remote user creates client with admin module | Remote with client functions |
| 2 | Client user creates admin, bypasses checks | Client with admin module |
| 3 | Admin modifies superadmin, gains superadmin | Admin |
| 4 | Superadmin injects PHP code via language editor | Superadmin |
The ISPConfig vulnerability chain demonstrates how seemingly minor logic and validation flaws can lead to full system compromise. Organizations using ISPConfig should review their user permissions and monitor for updates, as previous versions may also be affected.
In the current threat landscape, robust input validation and least-privilege principles are more crucial than ever for web hosting security.
.webp?w=696&resize=696,0&ssl=1)





