A critical vulnerabilities in Cisco Identity Services Engine (ISE), demonstrating how attackers can achieve complete system compromise with root access.
The vulnerabilities, tracked as CVE-2025-20281 and CVE-2025-20337, affect the pre-authentication phase and allow remote code execution without requiring valid credentials.
The vulnerability was initially reported to the Zero Day Initiative (ZDI) on January 25, 2025, by security researcher Kentaro Kawane of GMO Cybersecurity by Ierae.
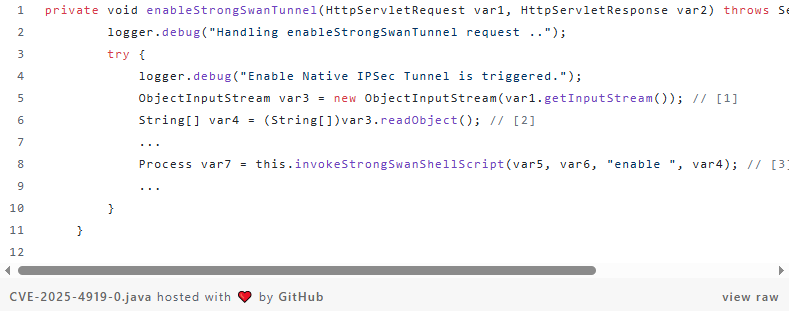
The vulnerability exists in the enableStrongSwanTunnel method of the DescriptionRegistrationListener class, where unsafe deserialization of untrusted data creates multiple attack vectors.
During analysis, researchers discovered that the same vulnerable function also contained a command injection vulnerability that executes with root privileges.
Cisco initially assigned both issues the same CVE identifier (CVE-2025-20281), but later released a separate advisory for CVE-2025-20337 to fully address the command injection component.
The company has since patched both vulnerabilities, though the distinct nature of the fixes suggests they may have been separate issues rather than duplicates.
The vulnerable code allows attackers to send malicious serialized Java objects to the /deployment-rpc/enableStrongSwanTunnel endpoint, where user-controlled input is passed directly to system commands executed via sudo /opt/CSCOcpm/bin/configureStrongSwan.sh.
Critical Cisco ISE Vulnerabilities
Exploitation of this vulnerability required overcoming several technical challenges, making it more complex than typical command injection attacks.
The primary obstacle involved Java’s StringTokenizer class, which processes the malicious input before passing it to the underlying bash script.
The exploitation path leads through a chain of function calls that ultimately execute attacker-controlled commands within a Docker container named strongswan-container.
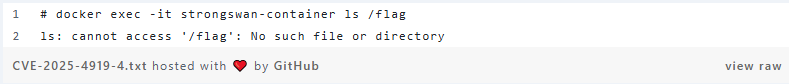
However, researchers discovered this container runs in privileged mode, enabling a container escape technique.
Using Linux cgroup manipulation and user-mode helpers, attackers can execute arbitrary commands on the host system with root privileges.
The final exploit payload involves base64-encoding a container escape script to avoid space character restrictions, then using the decoded script to mount cgroups, create release agents, and execute commands that establish persistent SSH access to the target system.
Mitigations
According to Report, Cisco ISE serves as a central authentication and authorization platform in many enterprise networks, making these vulnerabilities particularly dangerous for organizations.
The pre-authentication nature of the attack means that attackers do not need valid credentials to exploit affected systems, significantly lowering the barrier to successful compromise.
The combination of remote code execution and container escape capabilities allows attackers to achieve complete system takeover, potentially compromising network segmentation policies and accessing sensitive authentication data.
Organizations using affected Cisco ISE versions should immediately apply available security patches and review their network architecture to limit exposure of ISE management interfaces.
Security teams should also audit privileged container configurations and consider implementing additional monitoring for unusual cgroup activities and SSH access patterns that could indicate successful exploitation of these vulnerabilities.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




