As of early July 2025, security analysts at IBM X-Force are reporting an ongoing wave of sophisticated cyberattacks launched by the Russian-aligned threat actor Hive0156.
Targeting Ukrainian government offices and military personnel, Hive0156 is deploying the Remcos Remote Access Trojan (RAT) to gain persistent surreptitious access and build infrastructure for information theft and espionage.
Shifting Tactics: Decoys and Technical Evolution
For much of 2024 and early 2025, Hive0156 baited victims through emails and messaging apps with decoy documents containing military-sensitive themes, wartime losses, readiness checks, and operational staff distribution.
Recent operations suggest a tactical evolution: the group now lures users with more generic “petitions” or “official letters,” broadening their potential victim pool beyond the armed forces.
The attack chain begins with a seemingly innocuous Microsoft LNK shortcut or PowerShell script file.
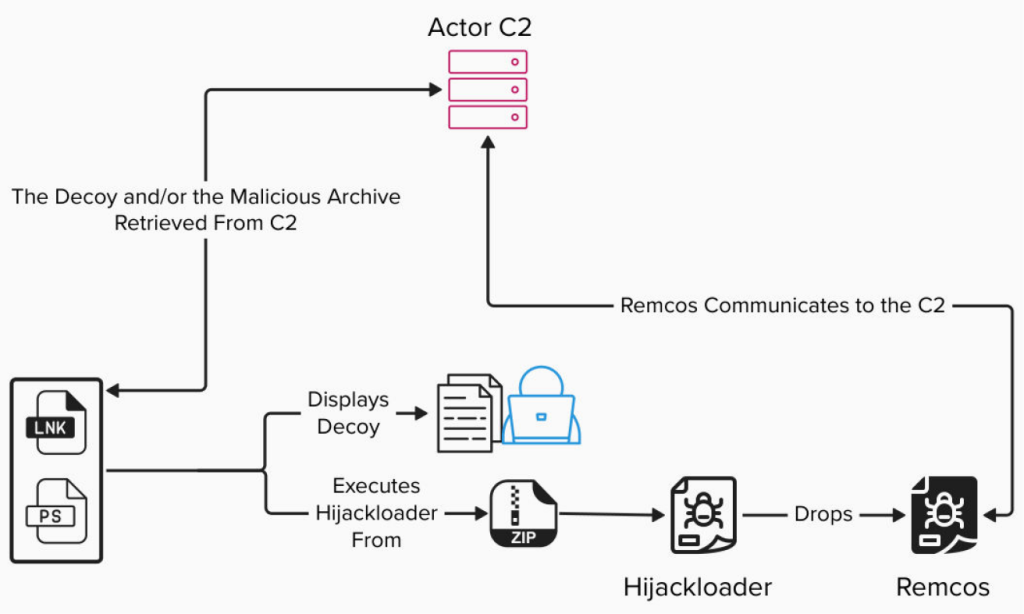
Once a user executes the file, it reaches out to the attacker’s command-and-control (C2) server, which typically filters access based on geographic region and device to evade detection.
The C2 then delivers the next stage: a ZIP archive loaded with malicious components and a corrupted decoy document.
Inside, a legitimate-looking executable (PortRemo.exe) and its required DLL files are bundled together with a poisoned, patched DLL (sqlite3.dll).
Upon launch, this DLL loads a modular loader, known as HijackLoader (also referred to as IDAT Loader), which decrypts additional payloads and launches the Remcos RAT, embedding itself deeply within the infected system.
Remcos RAT: Stealthy Foothold and Adaptive Surveillance
Once delivered, Remcos RAT activates its configuration, which is designed to evade detection and maintain control.
While Hive0156’s version utilizes limited enabled features to evade quick identification, Remcos comes packed with capabilities, including persistent access, process surveillance, keystroke logging, screen capturing, file exfiltration, browser credential theft, and granular remote control through its attacker-friendly GUI.
Remcos communicates with C2 infrastructure maintained by Hive0156 on servers worldwide, including those possibly sanctioned by Russian ISPs.
Analysts observed unique campaign identifiers in Remcos configurations, allowing attackers to run several parallel operations and manage infections efficiently.
Defensive Recommendations and Continued Vigilance
X-Force urges organizations and individuals associated with Ukraine’s government or military to heighten their cyber hygiene.
Proactive steps include endpoint protection upgrades, network segmentation, geo-blocking for high-risk IPs, rigorous user awareness training, and prompt patch management.
Special vigilance is warranted against suspicious LNK and PowerShell files, the most common initial vectors.
With Hive0156 evolving both its malware delivery and social engineering techniques, Ukrainian networks remain under constant cyber siege underscoring the critical need for robust, adaptive cyber defenses in conflict zones.
Indicators of compromise
| Indicator | Indicator Type | Context |
| 5.101.83[.]18 | IP Address | C2 |
| 5.101.83[.]19 | IP Address | C2 |
| 5.101.82[.]52 | IP Address | C2 |
| 146.185.239[.]11 | IP Address | C2 |
| 146.185.239[.]12 | IP Address | C2 |






