AhnLab Security Intelligence Center (ASEC) has uncovered a sophisticated cyberattack campaign leveraging weaponized shortcut (LNK) files, cleverly disguised as credit card security notifications.
The malicious file, named card_detail_20250610.html.lnk, masquerades as an official HTML pop-up for email authentication, targeting unsuspecting banking customers and prompting them to reveal sensitive personal information.
Multi-Stage Attack Chain Featuring Reflective DLL Injection
Upon execution, the .lnk file initiates a multi-stage payload delivery. Leveraging legitimate-looking HTML bait content, the attacker first downloads both an HTML decoy and a malicious HTA (HTML Application) script from a remote command-and-control (C2) server.
The HTML file, which visually replicates a credit card company’s security interface, serves as a distraction. At the same time, the HTA script silently orchestrates the next phase of infection in the Windows Temporary directory.
Execution of the HTA file results in the creation of two additional files within the user’s local profile directory: a malicious DLL named sys.dll and a text file, user.txt, which contains further URLs used for downloading a trio of payload DLLs (app, net, and notepad.log).
Using the Windows utility rundll32.exe, sys.dll is invoked to activate its malicious behavior.
What makes this campaign especially insidious is its employment of Reflective DLL Injection: all three payload DLLs are injected directly into memory, thus bypassing many conventional antivirus detections.
Extensive Data Theft and Keylogging Capabilities
Each injected DLL serves distinct malicious functions. The app DLL focuses on harvesting passwords and stored data from popular web browsers including Chrome, Brave, and Edge.
The net DLL expands the infostealing network to encompass additional browsers (Opera, Firefox) and even captures login credentials from web services such as Google, Yahoo, Facebook, and Outlook.
The notepad.log DLL is particularly dangerous, acting as a fully featured backdoor. It enables remote execution of shell commands, file collection and exfiltration, file downloading, and persistent keylogging.
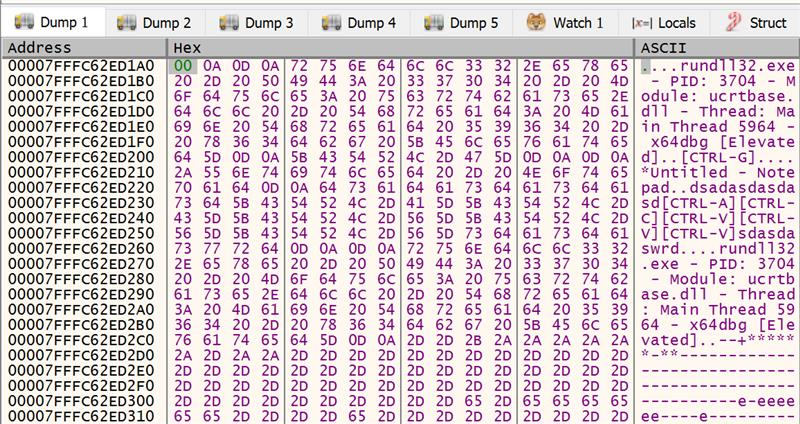
All logged keystrokes are stealthily stored in C:\Users \ {username}\AppData\Local\netkey, with evidence of keylogging scripts having been directly observed in system memory.
AhnLab warns that this attack may go unnoticed by victims, as legitimate decoy files are presented to divert suspicion while data is being stolen and exfiltrated in the background.
Ongoing LNK Campaigns: Heightened Vigilance Urged
Threat actors are continually innovating, using convincing spoofed emails and shortcut files to exploit user trust.
MD5 hashes linked to the identified files include 046aab6c2bcd4f87b70edd14330f326b, 71105e164f5838049aa9b1c634ab6047, and several others.
Users are strongly advised to verify the legitimacy of email attachments, especially those posing as banking or credit card security alerts, and to ensure their endpoint security software is up to date.
This latest campaign underscores the growing sophistication of cybercriminal tactics and the need for heightened vigilance among both enterprise and individual users.
IOCs
MD5
046aab6c2bcd4f87b70edd14330f326b
71105e164f5838049aa9b1c634ab6047
7110882e6d27b3296b1cd261064e4f81
94842649b102b5b7d605d254d3c03008
bf13ddd4bbff1aa69976e63cc966add






