A financially-motivated cybercriminal group dubbed “Greedy Sponge” has been systematically targeting Mexican organizations since 2021 with a heavily modified version of the AllaKore Remote Access Trojan (RAT), according to a new report from Arctic Wolf Labs.
The threat actor has recently upgraded its tactics to include advanced geofencing and secondary malware infections, making its operations more sophisticated and complex to detect.
Enhanced Attack Chain Targets Banking Credentials
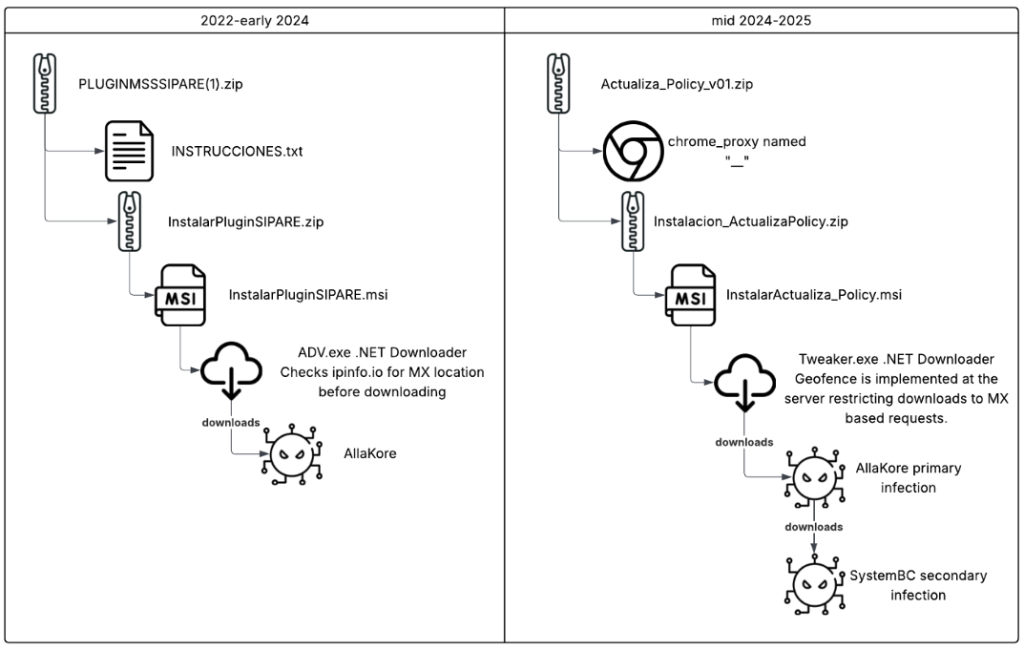
The latest campaign delivers malicious ZIP files containing trojanized Microsoft Installer (MSI) packages disguised as policy updates with Spanish filenames like “InstalarActualiza_Policy.msi”.
These packages deploy a .NET downloader called Gadget.exe, which subsequently fetches the customized AllaKore RAT payload from command-and-control servers hosted on Hostwinds infrastructure.
The modified AllaKore RAT now includes specialized functions explicitly designed to harvest banking credentials and authentication tokens.
Arctic Wolf researchers identified custom functions with labels like “{TOKEN}”, “{DESTRABA}”, and “{MENSAJE}” that structure stolen financial data for server-side processing.
This indicates a tiered operation where hands-on operators steal credentials and send them back to command-and-control servers for use in fraudulent banking operations.
A significant operational change involves moving geofencing controls server-side rather than within the initial malware payload.
Previously, the .NET downloader checked if victims were located in Mexico; however, this verification now occurs at the delivery infrastructure level, hindering detection efforts by security researchers.
SystemBC Adds Secondary Infection Layer
Since mid-2024, Greedy Sponge has incorporated SystemBC, a multi-platform proxy malware written in C, as a secondary infection vector.
The group deploys this through a User Account Control (UAC) bypass technique, utilizing Microsoft’s Connection Manager Profile Installer (CMSTP.exe), which is compiled from publicly available exploit code.
The attack chain now includes persistence mechanisms that place updated RAT versions in the system’s Startup folder, which are downloaded from endpoints such as “/z1.txt” on their command-and-control infrastructure.
Secondary infections are automatically downloaded to the victim’s AppData folder and executed immediately.
Arctic Wolf’s analysis reveals that all identified phishing sites emulate Mexican business websites and are hosted on the same Hostwinds server at IP address 142.254.133.54.
The group’s infrastructure spans multiple domains, including manzisuape[.]com for AllaKore C2 communications and pachisuave[.]com for SystemBC operations over port 4404.
Despite operating for over four years, security researchers classify Greedy Sponge as persistent but not particularly advanced.
However, their operational longevity suggests significant success in their financially motivated campaigns targeting Mexican entities across various industries, including banking, retail, manufacturing, and public sector organizations.
Indicators of Compromise (IOCs)
File IOCs
| SHA-256 | Type |
| 20fe630a63dd1741ec4ade9fe05b2e7e57208f776d5e20bbf0a012fea96ad0c0 | AllaKore |
| f76b456cf2af1382325c704bf70b5168d28d30da0f3d0a5207901277e01db395 | AllaKore |
| 4bf4bcf1cc45d9e50efbd184aad827e2c81f900a53961cf4fbea90fa31ca7549 | AllaKore |
| fed1c094280d1361e8a9aafdb4c1b3e63e0f2e5bb549d5d737d0a33f2b63b4b8 | AllaKore |
.jpg?w=696&resize=696,0&ssl=1)





