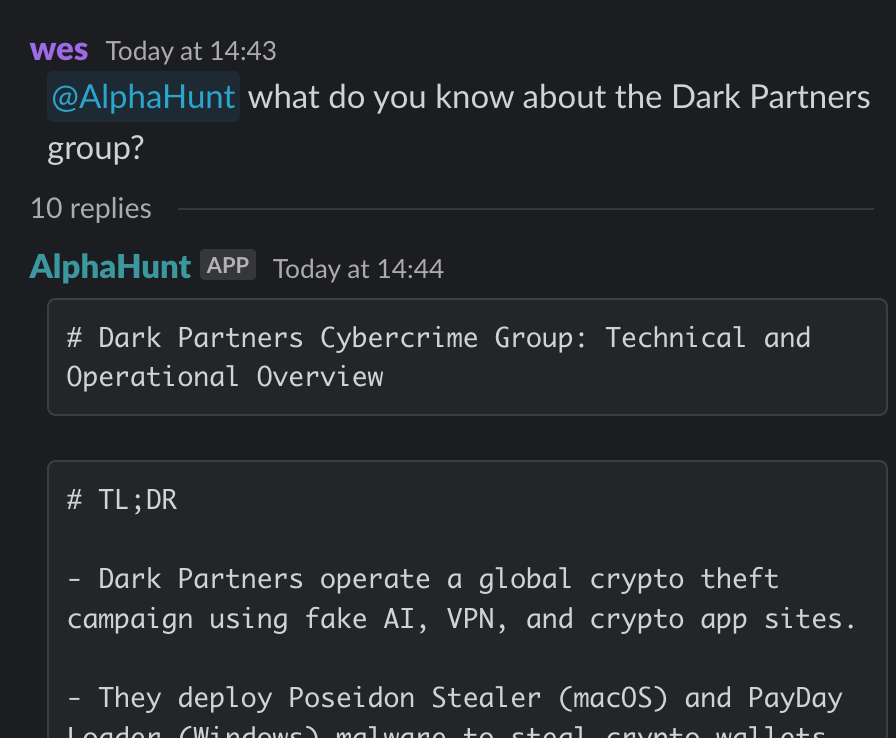
A sophisticated cybercrime group known as Dark Partners has been orchestrating large-scale cryptocurrency theft campaigns since May 2025, utilizing an extensive network of fake websites that impersonate popular AI tools, VPN services, and crypto wallet applications.
The financially motivated gang has established operations across the United States, European Union, Russia, Canada, and Australia, specifically targeting sectors rich in digital assets and credentials through advanced social engineering techniques and malware deployment.
Sophisticated Malware Arsenal Deployed Across Platforms
Dark Partners employs a dual-platform approach with two primary malware families: Poseidon Stealer for macOS systems and PayDay Loader for Windows environments.
Both malware variants utilize stolen code signing certificates to evade traditional security measures and incorporate anti-sandboxing capabilities to avoid automated analysis by security tools.
The group’s infrastructure spans nearly 250 fake domains designed to mimic legitimate software brands, with researchers identifying at least 37 impersonated applications ranging from cryptocurrency platforms to VPN services.
The PayDay Loader, specifically designed for Windows systems, establishes persistence through PowerShell scripts and virtual hard disks, while the macOS-targeting Poseidon Stealer utilizes launch agents and scheduled tasks.
Both malware families are centrally managed through the PayDay Panel, a sophisticated command-and-control platform that enables rapid payload deployment and operational scaling across the group’s global infrastructure.
Advanced Evasion Tactics Challenge Detection Systems
Cybercriminals demonstrate exceptional technical sophistication through their use of SEO poisoning techniques, which manipulate search engine results to promote their malicious websites above legitimate sources.
Their operations have been temporarily disrupted due to certificate revocations. Still, security researchers expect rapid adaptation through the acquisition of new code signing certificates and the expansion of their fake website network.
The group’s persistence mechanisms include PowerShell-based installation routines on Windows systems and the deployment of launch agents on macOS, making detection challenging for traditional signature-based security solutions.
Their anti-sandboxing measures specifically target automated analysis environments, requiring behavioral analytics and advanced endpoint detection capabilities for adequate identification.
Critical Defense Measures Required
Organizations must implement multi-layered security approaches to counter the evolving tactics of Dark Partners.
Essential defensive measures include advanced endpoint detection and response (EDR) systems with behavioral analytics capabilities, strict certificate validation protocols, and dynamic network controls that can adapt to new indicators of compromise.
Security teams should specifically monitor for macOS launch agents, Windows PowerShell persistence mechanisms, suspicious certificate usage patterns, and network traffic directed toward known command-and-control infrastructure.
The group’s continued evolution suggests the potential future adoption of more advanced evasion techniques, including fileless malware and living-off-the-land binaries, while potentially expanding its targeting to decentralized finance and NFT platforms.
Continuous intelligence sharing and user awareness training remain critical components of effective defense strategies against this persistent threat.
.jpg?w=696&resize=696,0&ssl=1)





