Security researchers from The DFIR Report, in collaboration with Proofpoint, have uncovered a resilient new variant of the notorious Interlock ransomware group’s remote access trojan (RAT).
This latest version, marking a significant shift from previous JavaScript-based Interlock RAT (also known as NodeSnake), is written in PHP and is now being deployed in a widespread and opportunistic campaign, primarily targeting Windows systems.
FileFix Variant: A New Intrusion Pathway
Since May 2025, investigators have linked Interlock RAT activity to threats stemming from the LandUpdate808 (aka KongTuke) web-inject clusters.
Attackers launch their campaign by compromising legitimate websites with single-line, hidden JavaScript injections. These scripts carefully filter incoming IPs and lure unwitting visitors into a multi-stage social engineering trap.
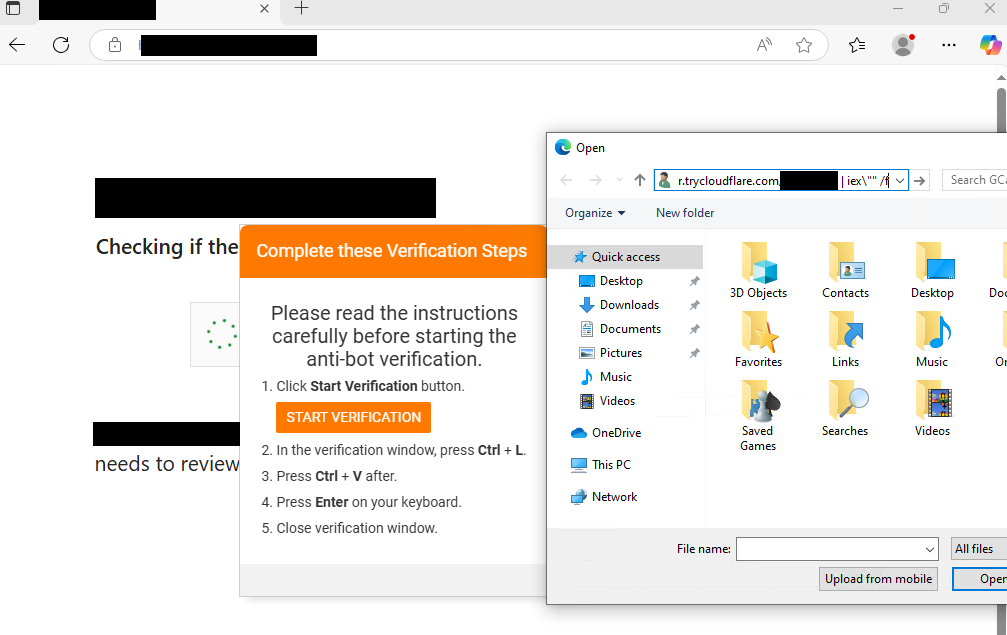
Victims are prompted to complete a “captcha” and then “verification steps,” which ultimately instruct them to paste a string into the Windows run command.
When executed, this triggers a PowerShell script responsible for fetching and deploying the PHP-based Interlock RAT.
A notable evolution is the FileFix variant’s role in delivering the RAT. The malware dropper leverages PowerShell to execute a locally deployed PHP interpreter residing within the user’s AppData directory.
It loads a configuration file containing operational directives, with suspicious command-line arguments and ZIP extension activation. Associated config files, such as config.cfg, have been observed with unique SHA256 hashes, signaling continued adaptation.
Stealthy Reconnaissance and Command & Control
Upon execution, the Interlock RAT immediately performs automated reconnaissance, issuing a suite of PowerShell commands to profile system information, enumerate processes and services, scan local drives, and probe the local network neighborhood.
Privilege checks determine if the malware is running as USER, ADMIN, or SYSTEM, allowing attackers to tailor further actions.
Further evidence suggests “hands on keyboard” activity, with attackers leveraging PowerShell and native commands for Active Directory enumeration, user and computer discovery, and session persistence.
Interlock RAT establishes a covert command and control channel via trycloudflare.com, abusing Cloudflare Tunnel for traffic obfuscation and resilience. Hardcoded fallback IP addresses ensure continued access if the primary tunnels are blocked.
The RAT is capable of downloading and executing additional payloads, running arbitrary commands, and setting up registry-based persistence. Post-compromise, attackers have been observed using RDP for lateral movement across victim environments.
Growing Threat Landscape
This campaign is indiscriminate, targeting a broad range of industries and organizations.
The emergence of a PHP-based Interlock RAT highlights the expanding technical sophistication of ransomware operators, who are increasingly leveraging common scripting languages and cloud services to evade detection.
Security organizations are urged to monitor for suspicious PHP process execution, PowerShell abuse, and connections to the listed Cloudflare Tunnel domains and fallback IPs.
As the threat actors continue to evolve their tactics, defenders should remain vigilant and ensure endpoint controls and network monitoring are up-to-date.
IOCs
Configs Name: config.cfg | File Size: 27392 Byte(s) SHA256: 28a9982cf2b4fc53a1545b6ed0d0c1788ca9369a847750f5652ffa0ca7f7b7d3 Name: config.cfg | File Size: 28268 Byte(s) SHA256: 8afd6c0636c5d70ac0622396268786190a4
.jpg?w=696&resize=696,0&ssl=1)





