AhnLab Security Intelligence Center (ASEC) has issued a critical warning about ongoing cyberattacks targeting unpatched GeoServer installations, with threat actors actively exploiting a remote code execution vulnerability to deploy cryptocurrency mining malware and backdoor tools.
The attacks have been confirmed in South Korea, with researchers identifying sophisticated malware campaigns that leverage the CVE-2024-36401 vulnerability to compromise both Windows and Linux environments running the popular open-source Geographic Information System (GIS) server.
Critical Vulnerability Enables Widespread Exploitation
The cyberattacks center around CVE-2024-36401, a remote code execution vulnerability discovered in GeoServer, a Java-based open-source platform used for spatial data processing.
Since the vulnerability’s disclosure in 2024, multiple threat actors have actively exploited this security flaw to install various malware strains.
Previous reports from Fortinet documented similar attack campaigns distributing GOREVERSE, SideWalk, Mirai, Condi, and CoinMiner malware.
Meanwhile, Trend Micro identified the Earth Baxia threat actor as using this vulnerability for spear-phishing operations against Taiwanese government agencies.
In the South Korean attacks, cybercriminals specifically targeted Windows environments running vulnerable GeoServer installations.
The attackers exploited the unpatched vulnerability to execute PowerShell commands, subsequently installing the NetCat networking utility and XMRig cryptocurrency mining software.
The attack chain demonstrates a sophisticated understanding of both Windows and Linux environments, with threat actors deploying platform-specific scripts to maximize their reach across various operating systems.
Technical Attack Analysis and Malware Deployment
The attack methodology reveals a multi-stage infection process beginning with PowerShell command execution through the CVE-2024-36401 vulnerability.
Attackers download and execute a PowerShell script called “adminc.ps1” to install NetCat, which functions as a reverse shell connecting to command-and-control servers at IP address 107.180.100.247.
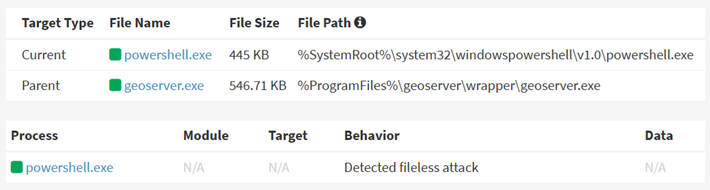
This backdoor access enables threat actors to maintain persistent control over compromised systems.
The XMRig cryptocurrency miner deployment utilizes both PowerShell and Bash scripts hosted on infrastructure at IP address 182.218.82.14.
The malware establishes persistence by modifying Cron jobs on Linux systems and configures mining operations to connect to the pool. Supportxmr.com is using hardcoded wallet credentials.
The mining configuration targets explicitly the Monero cryptocurrency, generating revenue for the attackers while consuming the victim’s system resources.
ASEC researchers have identified multiple indicators of compromise, including five distinct MD5 hashes and several malicious URLs used for payload delivery.
The attack infrastructure demonstrates careful planning, with separate scripts for Windows and Linux environments, ensuring maximum compatibility across diverse server deployments.
The Bash variant includes additional persistence mechanisms and process termination capabilities targeting competing cryptocurrency mining operations.
Organizations running GeoServer installations should immediately apply security patches addressing CVE-2024-36401 and conduct thorough security assessments to identify potential indicators of compromise.
The ongoing nature of these attacks highlights the crucial importance of keeping current security patches for internet-facing applications, especially those handling sensitive geospatial data.
.jpg?w=696&resize=696,0&ssl=1)





