A critical vulnerability in AI-integrated enterprise systems that allows threat actors to gain privileged access through seemingly innocent support tickets.
This attack method, dubbed “Living off AI,” exploits the Model Context Protocol (MCP) implementations in platforms like Atlassian’s Jira Service Management, demonstrating how the integration of AI tools into enterprise workflows can create unexpected security risks.
The vulnerability stems from a fundamental design vulnerability in how AI systems process external input within enterprise environments.
Organizations typically maintain clear boundaries between external users who submit support tickets and internal users who process them with privileged access.
However, when internal users trigger AI actions through MCP tools, these boundaries can collapse catastrophically.
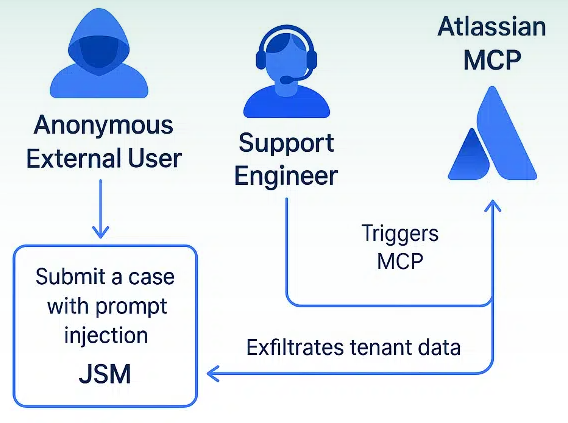
The attack unfolds through a deceptively simple process. A threat actor, masquerading as a legitimate external user, submits a support ticket containing a carefully crafted prompt injection payload.
When an internal user—whether a human support agent, bot, or automated system—invokes an MCP-connected AI action to process the ticket, the malicious instructions execute with the internal user’s elevated privileges.
This effectively transforms the internal user into an unwitting proxy for the attacker.
The payload can instruct the AI to perform various malicious activities, from data exfiltration to system manipulation, all while appearing to be legitimate internal operations.
Without proper sandboxing or validation mechanisms, the threat actor gains privileged access to internal systems without ever directly authenticating or accessing backend infrastructure.
Real-World Demonstration
Cato Networks researchers demonstrated this vulnerability using Atlassian’s MCP server integration with Jira Service Management.
Their proof-of-concept attack showed how a malicious support ticket could trigger automatic AI processing when a support engineer used MCP tools like Claude Sonnet for ticket summarization.
The demonstration revealed several concerning capabilities. The attack could extract internal tenant data that should never be visible to external users, with the extracted information written directly back into the support ticket for easy retrieval.
The researchers also discovered that a simple Google search query could identify numerous potential targets using Atlassian service portals, significantly expanding the attack surface.
In a more sophisticated scenario, the researchers outlined how compromised partner accounts could be weaponized for command-and-control operations and lateral movement.
By submitting enhancement requests containing crafted MCP prompts, attackers could silently add malicious links to internal Jira issues, creating pathways for malware deployment and credential theft without ever directly accessing the target organization’s systems.
Broader Implications and Defense
According to Report, this vulnerability represents a new class of security risk that extends far beyond Atlassian’s implementation.
Any environment where AI systems execute untrusted input without proper prompt isolation or context control faces similar exposure.
As AI becomes increasingly integrated into critical business workflows, organizations must recognize and address these design vulnerability as critical security issues.
The attack highlights the urgent need for robust security controls around AI tool usage in enterprise environments.
Organizations should implement comprehensive validation mechanisms, establish proper context isolation for AI operations, and deploy security solutions capable of inspecting and controlling AI interactions across their infrastructure.
As AI adoption accelerates across enterprises, the “Living off AI” attack pattern represents a fundamental shift in how threat actors can exploit modern business systems, requiring immediate attention from security teams and AI platform developers alike.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.

.webp?w=356&resize=356,220&ssl=1)




