Mobile device security remains a critical battleground, with Android the world’s most widely used mobile operating platform at the center of sophisticated attack campaigns.
While conventional malware grabs headlines, a more insidious threat is increasingly gaining traction: privilege escalation exploits leveraging legitimate OEM (Original Equipment Manufacturer) permissions.
These attacks are stealthy, powerful, and alarmingly effective.
1. Understanding OEM Permission Abuse: The Hidden Threat
Android’s robust security model was designed to compartmentalize app capabilities through fine-grained permission control.
However, device manufacturers routinely introduce custom permissions that grant “system-level” privileges to their apps.
For example, permissions such as “.permission._SECURITY” might permit modification of security policies, while “.permission._HW_CONTROL” could enable direct hardware interaction.
Other examples include “.permission.USE_INTERNAL_GENERAL_API,” which provides access to internal system APIs, or “android.permission.INTERACT_ACROSS_USERS_FULL,” allowing cross-user data access.
The catch: these permissions are often poorly documented and vaguely described, making their true power difficult to assess.
Threat actors have learned to harness them by impersonating system apps, compromising legitimate apps, or combining multiple OEM privileges for unintended and often malicious purposes.
This allows attackers to bypass standard Android permission restrictions, override user privacy settings, modify security configurations, and even access secure hardware features.
2. Real-World Exploits: From Accessibility APIs to Pre-Installed Apps
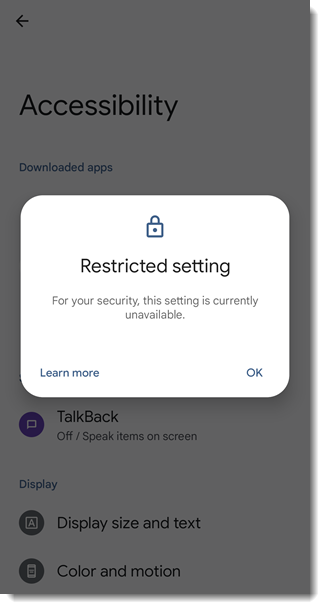
Recent research has illuminated several real-world attack vectors. For example, many threat actors target the Accessibility API, a powerful feature intended to help users with disabilities.
Malicious apps request Accessibility Service permissions and, once granted, can monitor user input, automate UI interactions, inject fake UI elements, and even install malware payloads without user intervention.
This abuse is particularly problematic for sideloaded apps, which bypass official app store security checks.
However, the threat doesn’t stop there. Even pre-installed (“privileged”) apps are vulnerable.
These apps, which are often impossible to uninstall, are included by device manufacturers for convenience but can be riddled with security flaws.
For instance, a popular OEM’s “Private Folder” app was found to contain an intent redirection vulnerability, allowing attackers to execute unauthorized privileged actions and access sensitive data, such as contacts, photos, and call logs, without user interaction.
3. How Organizations Can Defend Against Privilege Escalation
Defending against OEM permission abuse and privilege escalation requires proactive, multi-layered security strategies.
Traditional detection systems often fail to flag apps that acquire excessive privileges through legitimate channels, such as sideloading or OEM pre-installation.
To address this, organizations must implement comprehensive app vetting processes that analyze both static (permission requests, manifest declarations) and dynamic (runtime behavior, network communication) indicators.
Industry leaders like Zimperium utilize static code analysis to detect insecure API usage and hardcoded secrets, dynamic analysis to monitor runtime behaviors and identify permission abuse, and machine learning-powered risk scoring to flag suspicious applications.
These tools also assess pre-installed apps and detect sideloaded threats, ensuring that neither official nor unofficial apps can compromise enterprise security.
By enforcing least privilege and continuously monitoring for privilege escalation risks, organizations can protect their devices against these advanced, mobile-first attacks.
In summary, the abuse of OEM permissions is a growing, underappreciated threat in the Android ecosystem.
Only through vigilant app vetting, rigorous permission analysis, and proactive security practices can organizations and users hope to keep their devices and their data safe from increasingly creative attackers.
.webp?w=696&resize=696,0&ssl=1)





